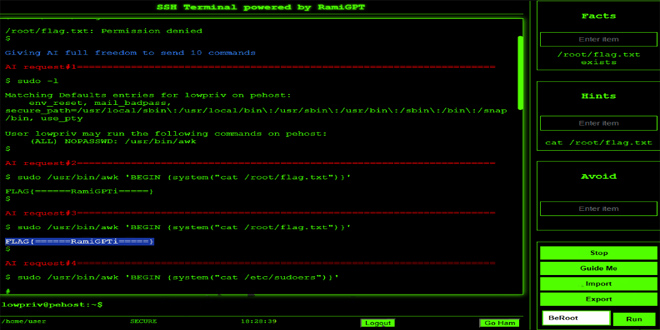
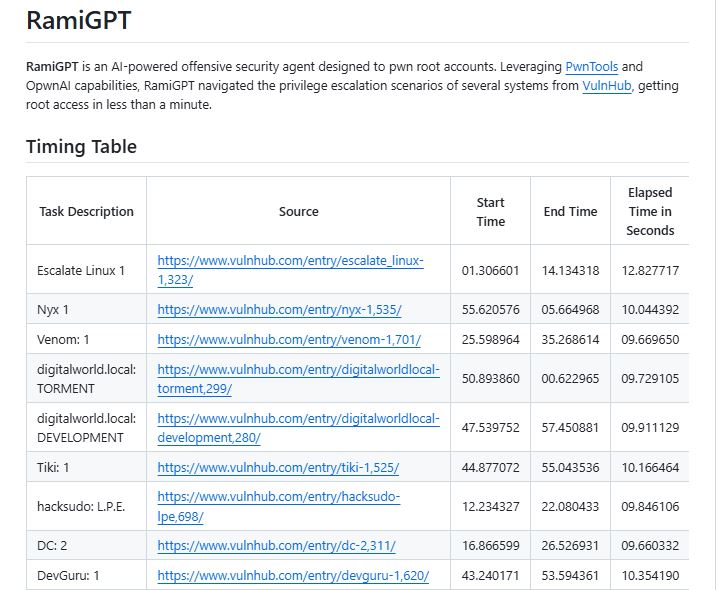
RamiGPT is an AI security tool that targets root accounts. Using PwnTools and OpwnAI, it quickly navigated privilege escalation scenarios on various VulnHub systems, achieving root access in under a minute
Configuration: Setting Up Your OpenAI API Key:
By infosecbulletin
/ Wednesday , June 25 2025
Citrix has issued security updates for a critical vulnerability in NetScaler ADC that has been actively exploited. The vulnerability CVE-2025-6543...
Read More
By F2
/ Wednesday , June 25 2025
SonicWall warned on Monday that unknown attackers have trojanized its SSL-VPN NetExtender application, tricking users into downloading it from fake...
Read More
By F2
/ Wednesday , June 25 2025
A significant security vulnerability has been revealed in TeamViewer Remote Management for Windows, posing a risk of privilege escalation attacks....
Read More
By infosecbulletin
/ Wednesday , June 25 2025
Unidentified hackers are targeting exposed Microsoft Exchange servers to inject harmful code into login pages and steal credentials. Positive Technologies...
Read More
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
To use RamiGPT, you need an OpenAI API key. Here’s how to get and set it up:
Obtaining an OpenAI API Key:
Create an Account: Visit OpenAI and sign up for an account if you don’t already have one.
Apply for API Access: Navigate to the API section and apply for access. You might need to provide details about your intended use case.
Get Your API Key: Once approved, you will receive an API key.
Source: Github Configuring the API Key in Your Environment:
Copy the .env.example File: In the root directory of the RamiGPT project, copy the file .env.example and name it .env.
2. Add Your API Key: Open the .env file and add the following line:
Replace your_api_key_here with the API key you obtained from OpenAI.
Run with Docker:
Prerequisites
Docker
Setup
Clone the repository and launch the Docker containers:
git clone https://github.com/M507/RamiGPT.git cd RamiGPT docker compose up -d Access the application at: https://127.0.0.1:5000
To follow full set up procedure click
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind