WhatsApp has patched a zero-click, zero-day vulnerability used to install Paragon’s Graphite spyware following reports from security researchers at the University of Toronto’s Citizen Lab.
The company addressed the attack vector late last year “without the need for a client-side fix” and decided not to assign a CVE-ID after “reviewing the CVE guidelines published by MITRE, and [its] own internal policies.”
“WhatsApp has disrupted a spyware campaign by Paragon that targeted a number of users including journalists and members of civil society. We’ve reached out directly to people who we believe were affected,” BleepingComputer reported.
“This is the latest example of why spyware companies must be held accountable for their unlawful actions. WhatsApp will continue to protect people’s ability to communicate privately.”
On January 31, after mitigating the zero-click exploit deployed in these attacks, WhatsApp notified roughly 90 Android users from over two dozen countries, including Italian journalists and activists, targeted with Paragon spyware to collect sensitive data and intercept their private communications.
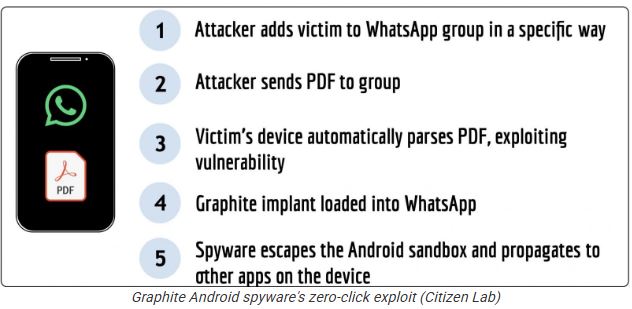
The researchers found that the attackers added the targets to a WhatsApp group before sending a PDF. In the next attack stage, the victim’s device automatically processed the PDF, exploiting the now-patched zero-day vulnerability to load a Graphite spyware implant in WhatsApp.
The implant later compromised other apps on the targeted devices by escaping the Android sandbox. Once installed, the spyware provides its operators access to the victims’ messaging applications.
Graphite spyware infections can be detected on hacked Android devices with the help of a forensic artifact (dubbed BIGPRETZEL) that can be spotted by analyzing compromised devices’ logs.
However, the lack of infection evidence doesn’t exclude the forensic indicators being overwritten or not captured because of “the sporadic nature of Android logs.”
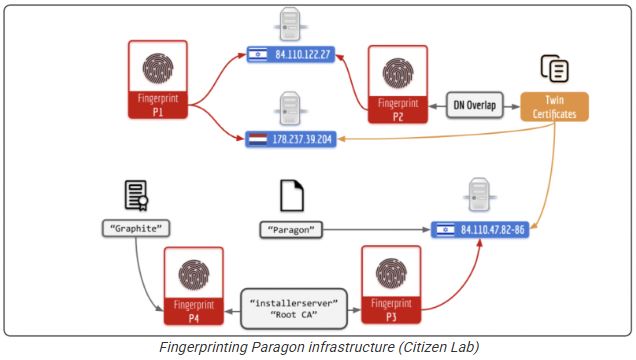
Citizen Lab also mapped out the server infrastructure used by Paragon to deploy the Graphite spyware implants on targets’ devices, finding potential links to multiple government customers, including Australia, Canada, Cyprus, Denmark, Israel, and Singapore.
Starting from the domain of a single server within Paragon’s infrastructure, the researchers developed multiple fingerprints that helped discover 150 digital certificates linked to dozens of IP addresses believed to be part of a dedicated command and control infrastructure.
“This infrastructure included cloud-based servers likely rented by Paragon and/or its customers, as well as servers likely hosted on the premises of Paragon and its government customers,” the researchers said.
“The infrastructure we found is linked to webpages entitled ‘Paragon’ returned by IP addresses in Israel (where Paragon is based), as well as a TLS certificate containing the organization name ‘Graphite, ‘which is the name of Paragon’s spyware, and the common name ‘installerserver’ (Pegasus, a competitor spyware product, uses the term’ Installation Server’ to refer to a server designed to infect a device with spyware).”
Israeli spyware developer Paragon Solutions Ltd. was founded in 2019 by Ehud Barak, the former Israeli Prime Minister, and Ehud Schneorson, the former commander of Israel’s Unit 8200. Florida-based investment group AE Industrial Partners reportedly acquired the company in December 2024.
Unlike competitors like NSO Group, Paragon claims it only sells its surveillance tools to law enforcement and intelligence agencies in democratic countries that want to target dangerous criminals.
In December 2022, the New York Times reported that the U.S. Drug Enforcement Administration (DEA) used the company’s Graphite spyware. Two years later, in October 2024, Wired reported that Paragon signed a $2 million contract with the U.S. Immigration and Customs Enforcement (ICE).
Report Credit: BleepingComputer
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind