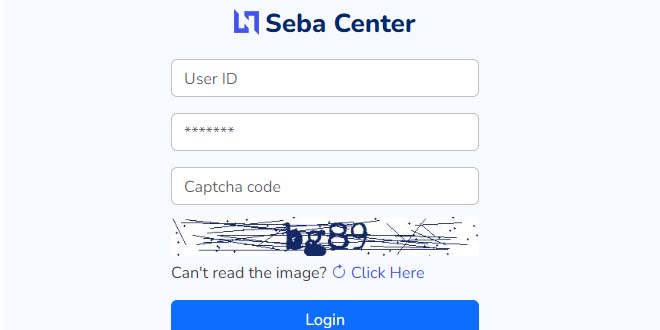
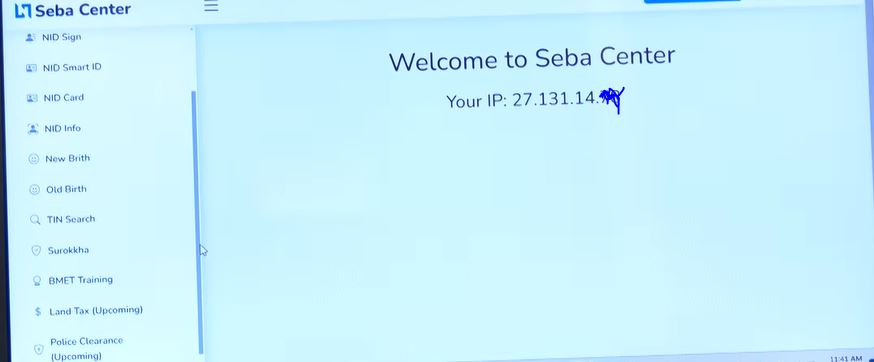
“sebacenter.xyz” is now a name of threat for personal identifiable information (PII) for the people of Bangladesh. By using only the site, miscreants are making and distributing fake paper of TIN, NID, NID info, BMET training, Surokkha, Death and birth register and duplicate land tax paper instantly. Even, if any NID number is entered, the detail of that person expose.
Counter terrorism and transitional crime (CTTC) of Dhaka metropolitan Police (DMP) seized the site and its four super admin and they are sent to prison but till now the site is active.
Imranul Islam, assistant commissioner of CTTC’s Cyber Crime Investigation Department, stated that most customers who used the fraudulent land tax services had not paid their taxes for 30 to 40 years, and used this scheme to evade tax.
He said the illegal business profits were shared equally among the super admins, while users or agents received commissions. Investigators found 360 fake land development tax payment receipts in one of the accounts.
He said, While in the remand of the fraudsters, CTTC got some crucial information of the racket. “Through an API the miscreants collect the information, its dangerous” stated he. We are working on the issue with utmost care.
Deputy Commissioner AFM Al Kibria of the Cyber Crime Investigation Department of CTTC revealed that the arrested individuals acquired the NID information from a government website. He emphasized the need for service providers to be more cautious when handling such sensitive information in order to prevent loopholes for fraudsters. Additionally, institutions should conduct regular IT audits, Vulnerability Assessment and Penetration Testing (VAPT), and system monitoring. On the other hand, people should also be cautious and avoid free services or offers, instead choosing legitimate service providers and websites.
Experts said, by using API the fraudsters collect the information. So, the proper authority must take stern action to identify which API is being used to do that and bring them under trial.
Various local media report about 176 organizations have access to the NID server while as of October 2023, the country’s NID server had information of about 12 crore voters, of whom around 5.5 crore have smart NID cards.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind