Today, software supply chain security management company Lineaje, released a new report titled “What’s in Your Open-Source Software?” that found 82% of open-source software components are “inherently risky” due to a mix of vulnerabilities, security issues, code quality or maintainability concerns.
The report highlighted that while more than 70% of software in the enterprise is open source, these elements often aren’t tracked, maintained, updated or inventoried, leaving serious vulnerabilities in the software supply chain for threat actors to exploit.
By infosecbulletin
/ Wednesday , September 10 2025
Sophos fixed an authentication bypass vulnerability in its AP6 Series Wireless Access Points, preventing attackers from obtaining admin privileges. The...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Security researcher Jeremiah Fowler discovered a database containing sensitive information from gym customers and staff, including names, financial details, and...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Microsoft patched September 2025 Patch Tuesday 81 flaws, including two publicly disclosed zero-day vulnerabilities. This Patch Tuesday addresses nine critical...
Read More
By infosecbulletin
/ Tuesday , September 9 2025
Elastic reported a security incident caused by a breach at Salesloft Drift, leading to unauthorized access to an internal email...
Read More
By infosecbulletin
/ Tuesday , September 9 2025
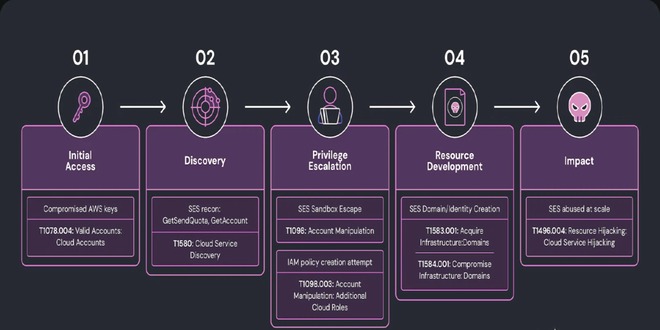
Researchers at Wiz discovered a complex phishing campaign using Amazon's Simple Email Service (SES) for large-scale attacks, showing how hacked...
Read More
By infosecbulletin
/ Monday , September 8 2025
The global ransomware landscape continues to shift in 2025, with SafePay rapidly emerging as one of the most active and...
Read More
By infosecbulletin
/ Sunday , September 7 2025
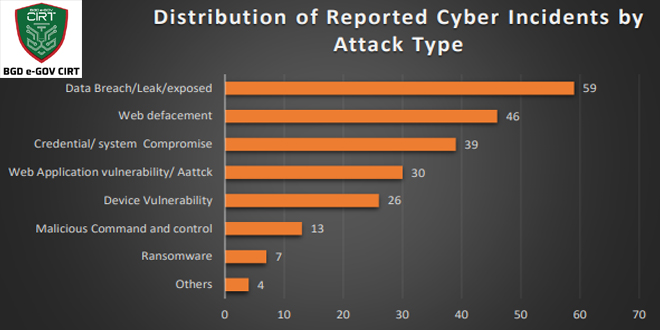
Bangladesh Cyber Threat Landscape 2024, by BGD e-GOV CIRT, reveals a sharp escalation in cyber threats across Bangladesh. The year...
Read More
By infosecbulletin
/ Sunday , September 7 2025
Investigations into the Nx "s1ngularity" NPM supply chain attack have unveiled a massive fallout, with thousands of account tokens and...
Read More
By infosecbulletin
/ Saturday , September 6 2025
ISC2 has launched a Threat Handling Foundations Certificate to assist cybersecurity experts in enhancing Digital Forensics and Incident Response (DFIR)...
Read More
By infosecbulletin
/ Thursday , September 4 2025
Jeremiah Fowler, a cybersecurity researcher, found an unprotected server revealing 378 GB of Navy Federal Credit Union files, including operational...
Read More
This comes less than a week after CISA called for software vendors to take action to implement “secure-by-design” development processes to ship code that’s secure “out of the box.”
Lineaje also found significant risk among widely-used open-source solutions, analyzing the top 44 popular projects of the Apache Software Foundation and discovering that 68% of dependencies are from non-Apache Software Foundation open-source projects, many with opaque origin and update mechanisms.
“It’s imperative that organizations today understand that open-source software has risks and is tamperable, even if it is very popular or provided by an established brand,” said Javed Hasan, CEO and cofounder of Lineaje.
“With more software being assembled than built, it’s become more important than ever to have formal tools to discover software DNA. Developers do not have X-ray vision to see inside a software component they include nor are most open-source selectors security experts,” Hasan said.
Given that 64% of all vulnerabilities have no fixes available yet, and can’t be patched, the report echoes CISA’s call for organizations to be more proactive about managing open-source risk. It also recommends that organizations deploy supply chain management tools that have the ability to assess the dynamic inherent risk and integrity of individual dependencies and projects.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind