The worm was first discovered in a 2023 post by security firm Sophos. It became active in 2019 when a variant of malware called PlugX added a feature to infect USB drives automatically. This allowed the malware to spread to new machines without needing any user interaction.
Sekoia, a European cybersecurity SAAS company reports that over 90,000 unique IP addresses are still infected with a PlugX worm variant, which spreads through infected USB drives and can bypass air gaps.
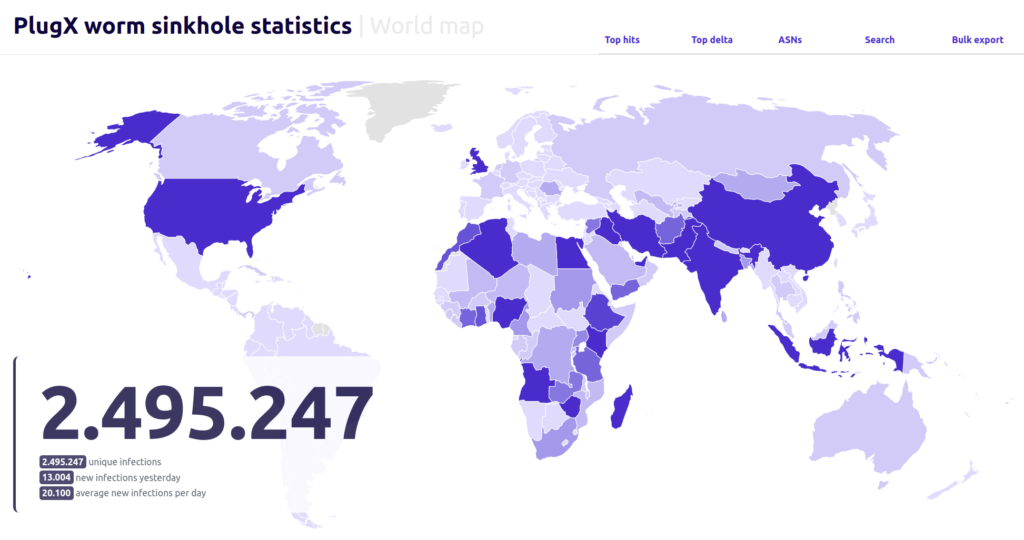
In the last six months, Sekoia has been tracking connections to a sinkholed IP associated with the worm. They have identified over 2.5 million IP addresses that connected to it.
Between 90,000 and 100,000 unique IPs keep sending requests to the sinkhole every day, indicating that the botnet is still active despite its operators losing control.
However, “anyone with interception capabilities or taking ownership of this server can send arbitrary commands to the infected host to repurpose it for malicious activities,” Sekoia says.
The PlugX remote access trojan has been around since 2008, but a self-spreading variant was released in 2020 by a threat actor known as Mustang Panda, likely to steal data from offline networks.
The worm puts a Windows shortcut file with the drive’s name and three files for DLL sideloading on the connected flash drive. These files include a real program, a harmful library, and a data file within the drive’s hidden RECYCLER.BIN folder. It also moves the drive’s contents to a new folder.
When the user opens the shortcut file, the malware opens a new window showing the drive’s contents, copies itself to the system, and creates a new registry key to stay active. Then, it starts again from the system and looks for USB drives to infect every 30 seconds.
The self-spreading technique used by the botnet has caused it to spread rapidly across networks. As a result, the botnet’s operators may have been forced to abandon the command-and-control server because it was unable to handle the large number of infected hosts.
Sekoia took control of a C&C IP address that was no longer being used. They then set up the necessary infrastructure to manage connection attempts and track where they originated from.
The security company found about 2.5 million infected computers in over 170 countries. They also noticed that the worm was still spreading at a rate of 20,000 infections per day.
The investigation only uses IP addresses, so it cannot determine the exact number of infected systems. This is because some IP addresses may be used by multiple workstations, and some systems may have dynamic IPs.
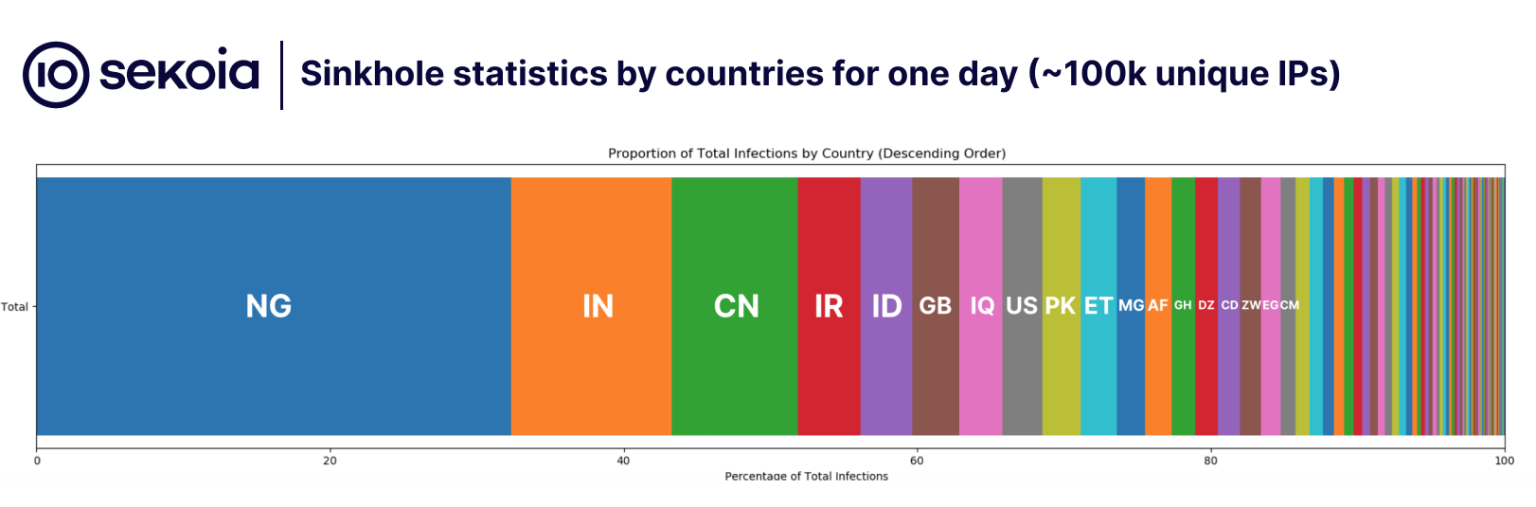
In April, the security company found over 100,000 different IP addresses connecting to the sinkhole. The majority of the victims are in countries that China’s Belt and Road Initiative considers strategically important.
“It is plausible, though not definitively certain as China invests everywhere, that this worm was developed to collect intelligence in various countries about the strategic and security concerns associated with the Belt and Road Initiative, mostly on its maritime and economic aspects,” Sekoia notes.
The company found a way to remove the PlugX variant malware from all infected hosts using a self-delete command.
An infected USB drive connected to an infected computer during disinfection can be cleaned, and the users’ files on those drives restored by delivering a crafted payload.
The worm might not be completely removed because it stays on infected flash drives and air-gaped systems without a way to get rid of it.
Sekoia contacted CERTs and law enforcement agencies in the affected countries, sharing data from the sinkhole and asking them to decide if disinfection should be done due to legal concerns.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














