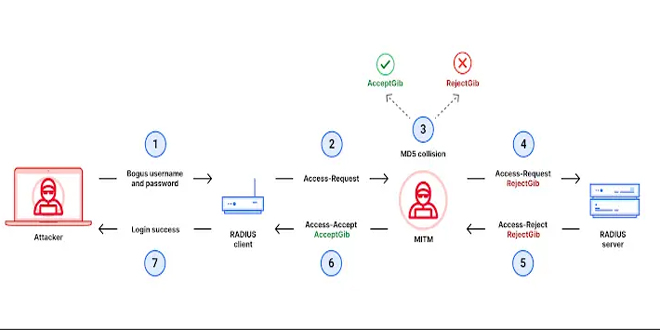
Cisco has issued a security advisory (CVE-2024-3596) in the RADIUS protocol, which is widely used for network access authentication and authorization. This vulnerability could let an attacker bypass multi-factor authentication (MFA) and gain unauthorized network access.
The vulnerability is due to a problem in the MD5 Response Authenticator signature in the RADIUS protocol. An attacker with network access can exploit this to bypass authentication and gain unauthorized access to sensitive network resources.
Cisco has confirmed that a wide range of its products are affected by this vulnerability, including:
Network and Content Security Devices:
Adaptive Security Appliance (ASA) (CSCwk71992)
Firepower Device Manager (FDM) (CSCwk69454)
Firepower Management Center (FMC) Software (CSCwk71817)
Ezoic
Firepower Threat Defense (FTD) Software (CSCwk67902)
Identity Services Engine (ISE) (CSCwk67747)
Secure Email Gateway (CSCwk70832)
Secure Web Appliance (CSCwk70834)
Network Management and Provisioning:
Application Policy Infrastructure Controller (APIC) (CSCwk70836)
Crosswork Change Automation (CSCwk70850)
Nexus Dashboard (CSCwk70840)
Routing and Switching – Enterprise and Service Provider:
ASR 5000 Series Routers (CSCwk70831)
Catalyst SD-WAN Controller (CSCwk70854)
Unified Computing:
UCS Central Software (CSCwk71967)
UCS Manager (CSCwk70842)
Cisco has confirmed that the following products are not affected by this vulnerability:
Nexus Dashboard Insights
Secure Workload
Firepower 4100/9300 FXOS Firepower Chassis Manager
Secure Malware Analytics Appliance
Umbrella Active Directory (AD) Connector
Cisco Evolved Programmable Network Manager (EPNM)
DNA Spaces Connector
Policy Suite
Ultra Cloud Core – Policy Control Function
UCS B-Series Blade Servers
Various Aironet and Catalyst series access points and wireless LAN controllers
The Cisco Product Security Incident Response Team (PSIRT) is aware of proof-of-concept exploit code available for this vulnerability but has not detected any malicious exploitation in the wild.
Cisco advises customers to promptly apply the available patches for their affected products. There are no workarounds for this vulnerability.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind