The Pakistan Ministry of Information Technology and Telecommunication has given permission to the Inter-Services Intelligence (ISI) to intercept citizens’ phone communications for national security reasons.
Issued on Monday, the ministry’s notification — a copy of which is available with Dawn.com — said that the authorisation was granted to the ISI under Section 54 of the Pakistan Telecommunication (Re-organisation) Act, 1996.
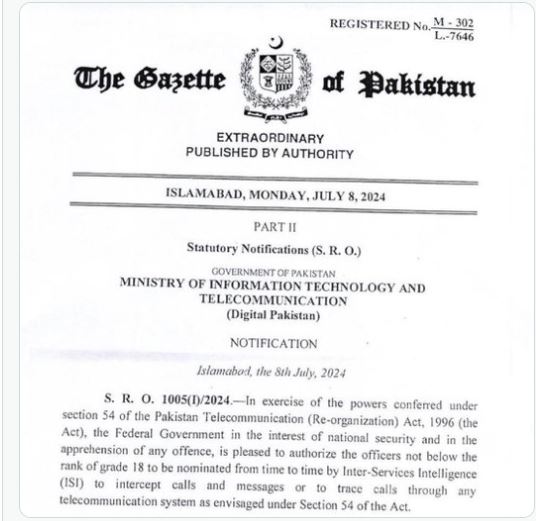
The notification read, “In exercise of the powers conferred under Section 54 … the federal government in the interest of national security and in the apprehension of any offence, is pleased to authorise the officers not below the rank of grade 18 to be nominated from time to time by the Inter-Services Intelligence (ISI) to intercept calls and messages or to trace calls through any telecommunication system as envisaged under Section 54 of the Act,”.
In December, the Islamabad High Court (IHC) was told during a case hearing about audio leaks that the government had not authorized any intelligence agency to monitor audio conversations.
The Attorney General for Pakistan, Mansoor Usman Awan, informed the high court during a hearing. The hearing was about a petition filed by Bushra Bibi, the spouse of former premier Imran Khan. In the petition, she was seeking action against a leaked conversation, which allegedly featured her and PTI leader Latif Khosa.
On Dec 6, the former first lady went to the IHC and argued that the recording violated her right to dignity and privacy, as stated in Article 14 of the Constitution.
The application was filed in the IHC by Khosa. The principal secretary to the prime minister and the secretaries of defense and interior were cited as respondents.
In May, Justice Babar Sattar stated that no state official is allowed to surveil citizens, and anyone doing so or helping in any way would be “liable for offences”.
The government authorized the intelligence agency to intercept calls and messages or trace a call for national security purposes or to catch criminals. Cellular companies are also not allowed to share citizens’ data with agencies.
The minister mentioned that it’s not a new law, but rather a modification of Section 54 of the Pakistan Telecommunication Reorganization Act of 1996.
He said no previous successive governments had changed this provision and still it was intact.
Section 54 of the act says, “Notwithstanding anything contained in any law for the time being in force, in the interest of national security or in the apprehension of any offence, the federal government may authorise any person or persons to intercept calls and messages or to trace calls through any telecommunication system.”
The minister said that the government periodically issued notifications regarding this, adding that many incidents occurred and individuals involved in serious crimes were caught through call interception by intelligence agencies under the same law.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind