The LockBit ransomware group reactivated a hidden website on the dark web. They posted a long message written by their leader, who vowed not to retreat from the criminal underground world.
The LockBit leader says the FBI used a vulnerability in PHP to hack their servers. They didn’t fix it because they became lazy after making a lot of money for 5 years.
Law enforcement did not take down backup servers that didn’t have PHP installed, LockBit said.
“All FBI actions are aimed at destroying the reputation of my affiliate program, my demoralization, they want me to leave and quit my job, they want to scare me because they can not find and eliminate me, I can not be stopped, you can not even hope, as long as I am alive I will continue to do pentest with postpaid,” the missive states.
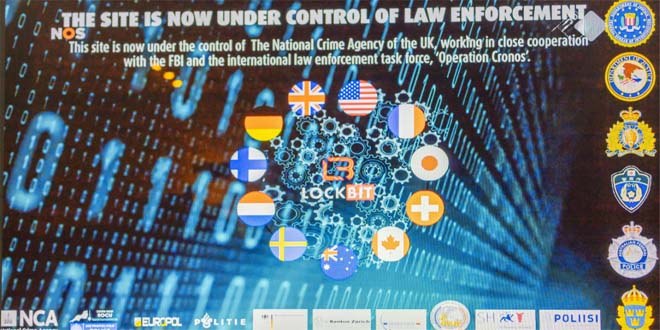
Law enforcement agencies participating in “Operation Cronos” said they would disclose the identity of LockBit leader, LockBitSupp, on Friday, but they didn’t. Instead, authorities stated on the seized leak site that they know who he is, where he lives, and how much he is worth.
According to Allan Liska from Recorded Future, LockBit has been heavily affected by this takedown. His previous sense of invincibility has been permanently shattered. Since then, his actions appear to be more of someone pretending to be in control, rather than someone who is actually in control of the situation.
The leak site that was re-established has victim entries that were apparently made just before Operation Cronos executed the takedown. One of the entries is for Fulton County, Ga. LockBit had previously claimed responsibility for an attack in January that disrupted the county court and tax systems. County District Attorney Fani Willis is pursuing a case against former President Donald Trump and 18 co-defendants for allegedly attempting to stop the transition of presidential power in 2020.
The LockBit message says the FBI might have used a PHP zero day, seized 1,000 of the 20,000 ransomware decryptors on the LockBit server, and the takedown was to stop the leaking of documents stolen from Fulton County.
LockBit: the gang’s all here
A post on X by malware repository vx-underground, who is openly in regular contact with both LockBit and its contemporary ALPHV/BlackCat, also insinuated the gang is off life support and still breathing.
“We asked Lockbit ransomware group administration their thoughts on this past week,” vx-underground posted on X Friday.

“Lockbit ransomware group said they will make formal reply to law enforcement once they’re finished restoring their infrastructure,” the post stated.
The post also included a comment from the notorious ALPHV/BlackCat ransomware group, who has been openly making fun of the LockBit seizure all week.
“My Mercedes drives Lockbit,” ALPHV told the repository, an obvious slam towards LockBit’s leader LockBitSupp.
The statement clearly referencing a post released by by law enforcement Friday claiming to have intimate knowledge about the gang leader and the car he drives.
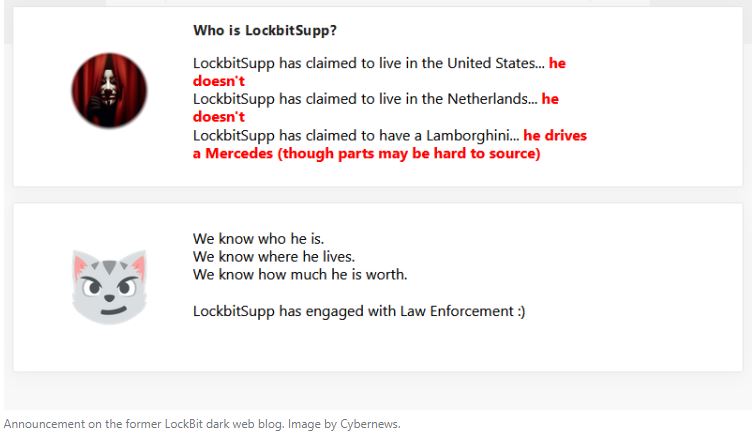
“Who is Lockbit Supp?,” authorities posted on the former LockBit dark web blog, now controlled by UK National Crime Agency (NCA), Interpol, and the FBI, among others.
One answer mockingly reads, “LockbitSupp has claimed to have a Lamborghini …”
Law enforcement then continues to answer its own question, “… he drives a Mercedes, (though parts may be hard to source)” it said in bright red lettering.
Source: Cybernews, bankinfosecurity
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind