The U.K. National Crime Agency (NCA) confirmed that it got LockBit’s source code and gathered intelligence about its activities and affiliates as part of Operation Cronos.
“Some of the data on LockBit’s systems belonged to victims who had paid a ransom to the threat actors, evidencing that even when a ransom is paid, it does not guarantee that data will be deleted, despite what the criminals have promised,” the agency said.
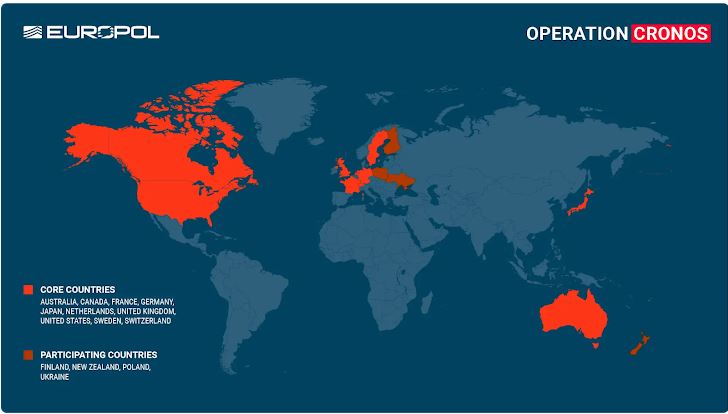
Two LockBit actors were arrested in Poland and Ukraine. More than 200 cryptocurrency accounts related to the group have been frozen. In the U.S., indictments were unsealed against two additional Russian individuals accused of conducting LockBit attacks.
The U.S. Department of Justice (DoJ) has accused Artur Sungatov and Ivan Gennadievich Kondratiev (also known as Bassterlord) of using LockBit to target multiple victims in the U.S., including businesses in the manufacturing and other industries. They have also targeted victims in the semiconductor and other industries worldwide.
Kondratyev has been charged with three criminal counts for using the Sodinokibi (also known as REvil) ransomware to encrypt data, steal victim information, and extort a ransom from a company in Alameda County, California.

The development comes in the aftermath of an international disruption campaign targeting LockBit, which the NCA described as the “world’s most harmful cyber crime group.”
The agency said it has taken control of LockBit’s services and infiltrated their entire criminal operation. This includes the environment used by affiliates and the leak site hosted on the dark web.
34 servers belonging to LockBit affiliates have been taken down. Over 1,000 decryption keys have been retrieved from the seized LockBit servers.
LockBit Ransomware Operation Shut Down:
LockBit, since its debut in late 2019, operates a ransomware-as-a-service (RaaS) scheme where affiliates are licensed to use the encryptors and execute the attacks in exchange for a percentage of the ransom.
The attacks use a tactic called double extortion. This tactic involves stealing sensitive data before encrypting it. The attackers then pressure the victims to pay a ransom to decrypt their files and prevent the data from being published.
LockBit Ransomware Operation Shut Down:
“The ransomware group is also infamous for experimenting with new methods for pressuring their victims into paying ransoms,” Europol said.
“Triple extortion is one such method which includes the traditional methods of encrypting the victim’s data and threatening to leak it, but also incorporates distributed denial-of-service (DDoS) attacks as an additional layer of pressure.”
Data theft was made easier with a tool called StealBit. The authorities from three countries, including the U.S., have seized the infrastructure used to steal and transfer victim data.
Eurojust and the Department of Justice report that LockBit attacks have impacted 2,500 victims worldwide, resulting in over $120 million in illicit profits. A free decryption tool is now available through No More Ransom to help recover files encrypted by the ransomware.
“Through our close collaboration, we have hacked the hackers; taken control of their infrastructure, seized their source code, and obtained keys that will help victims decrypt their systems,” NCA Director General Graeme Biggar said.
“As of today, LockBit are locked out. We have damaged the capability and most notably, the credibility of a group that depended on secrecy and anonymity. LockBit may seek to rebuild their criminal enterprise. However, we know who they are, and how they operate.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind













