Morphisec Threat Labs researchers have recently exposed a sneaky loader called “in2al5d p3in4er” (Invalid Printer) that delivers Aurora information stealer malware through YouTube videos.
Late in 2022, Aurora appeared on the threat landscape for the first time, and it’s an information stealer written in Go programming language.
Abusing YouTube as a Distribution Platform
Aurora is a commodity malware distributed through fake cracked software download sites and YouTube videos to other threat actors looking to use it.
YouTube has become an attractive distribution platform for threat actors looking to spread malware to access sensitive information.
Due to its mass popularity, YouTube has become one of the first choices for threat actors.
Hackers have found a new way to spread malware by hacking popular YouTube accounts and posting videos with malicious links or downloads through those compromised accounts or channels.
While the hackers also use optimized SEO tags to boost the visibility of videos in search results, which will increase the click-through rate (CTR).
Since threat actors are actively generating handsome revenue by stealing YouTube accounts for a fee, these services are now actively marketed by hackers in several underground forums and marketplaces.
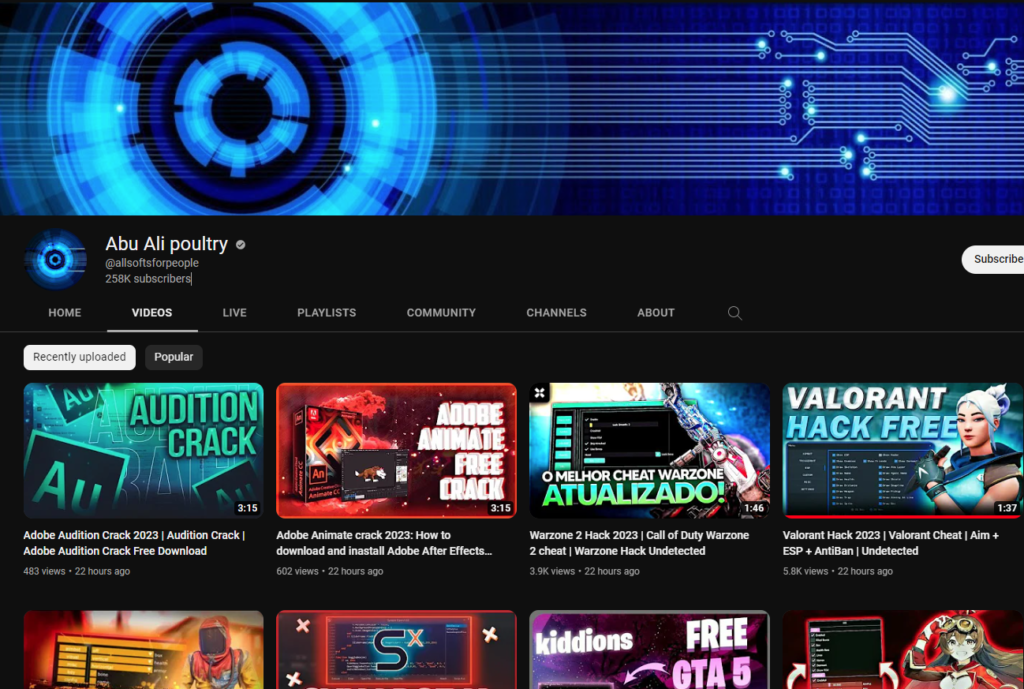
Artificial intelligence (AI) is used by the service to generate videos, making it easier and quicker to create budget-backed content that looks convincing.
Victims who click on the links in YouTube video descriptions are taken to fake websites that trick them into downloading malware disguised as legitimate software.
To appear legitimate, these fake websites use the following things to create the illusion that they are real:-
- Similar URLs
- Similar logos
- Similar branding
These decoy websites convince users to download applications containing malware and trick them into entering their sensitive or personal information.
Technical analysis
Morphisec asserted that this loader checks the vendor ID of a system’s graphics card and terminates itself if the value doesn’t match a list of approved IDs, which includes:-
- AMD
- Intel
- NVIDIA
Using a technique called “process hollowing,” the loader decrypts the final payload and injects it into a genuine process called “sihost.exe.”
While injecting the final payload into the legitimate process, the loader dynamically decrypts all the required Windows API and uses the XOR key ‘in2al5d p3in4er‘ to decrypt the API names.
The loader employs Embarcadero RAD Studio to create executable files that can be used on various platforms, which helps it evade detection by security software.
Malware loaders like in2al5d p3in4er are the building blocks of an attack, providing an initial foothold between the attacker and the compromised system.
They serve as a crucial first stage, facilitating the delivery of more complex and damaging payloads.
The threat actors are responsible for in2al5d p3in4er malware are leveraging social engineering tactics and using them in combination with the malware to create a significant impact.
They target popular YouTube accounts to redirect the viewers to fake and legitimate-looking websites.
To prevent attacks from in2al5d p3in4er, educating employees about identifying social engineering schemes is crucial.
Source: Cybersecuritynews
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind