In late 2023, Sygnia researchers investigated a cyber incident involving a major organization that was reportedly caused by a threat group known as ‘Velvet Ant.’
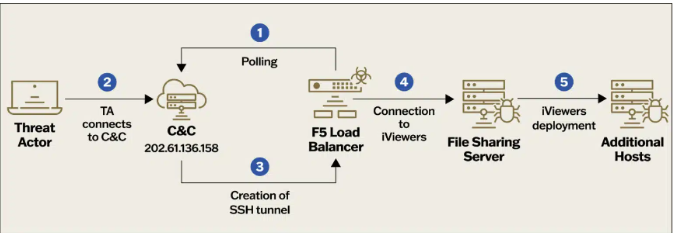
The cyberspies deployed custom malware on F5 BIG-IP appliances to gain persistent access to the internal network of the target organization and steal sensitive data.
The investigation found that malicious actor had been in the organization’s network for years to gather information. They managed to stay in the network by creating several entry points.
One method used was to take advantage of an old F5 BIG-IP device that was connected to the internet. It was used as a way to control the target’s network from the inside. When one way in was found and fixed, the attacker quickly found and used a different way. This showed how quickly they could adapt and how well they knew the target’s network.
The analysis published by Sygnia reads, “The compromised organization had two F5 BIG-IP appliances which provided services such as firewall, WAF, load balancing and local traffic management. These appliances were directly exposed to the internet, and both of which were compromised. Both F5 appliances were running an outdated, vulnerable, operating system. The threat actor may have leveraged one of the vulnerabilities to gain remote access to the appliances.” “As a result, a backdoor hidden within the F5 appliance can evade detection from traditional log monitoring solutions.”
Once the attackers compromised the F5 appliances, they gained access to internal file servers and deployed the PlugX RAT.
Forensic analysis of the F5 appliances identified four binaries deployed by the threat actor:
VELVETSTING – A tool connects to the threat actor’s command and control center once an hour to search for commands to execute. When the tool receives a command, it is executed using ‘csh’ (Unix C shell).
VELVETTAP – a tool with the ability to capture network packets.
SAMRID – The tool named ‘EarthWorm’ is an open-source SOCKS proxy tunneller available on GitHub. It has been used in the past by several China-linked APT groups, including ‘Volt Typhoon’, ‘APT27’, and ‘Gelsemium’.
ESRDE – a tool with slight differences compared to ‘VELVETSTING’
Researchers provided the following recommendations for organizations to mitigate attacks of groups like Velvet Ant:
Restrict outgoing internet data flow.
Reduce lateral movement in the network.
Improve the security measures for old servers.
Mitigate credential harvesting.
Protect public-facing devices.
The report includes indicators of compromise for the analyzed attack.
(Media Disclaimer: This report is based on research conducted internally and externally using different ways. The information provided is for reference only, and users are responsible for relying on it. Infosecbulletin is not liable for the accuracy or consequences of using this information by any means)
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














