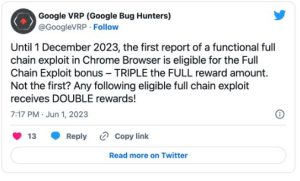
Google is temporarily offering a triple reward to bug bounty hunters who report functional full-chain exploits that can escape the Chrome browser’s sandbox. The bonus is effective until December 1, 2023.
A sandbox is a security feature that isolates code from the rest of the system, making it more difficult for attackers to exploit vulnerabilities. A full-chain exploit is a series of vulnerabilities that can be chained together to escape the sandbox and gain control of the system.
Google is offering the bonus to encourage security researchers to find and report these types of vulnerabilities. By identifying and fixing these vulnerabilities, Google can make Chrome more secure and protect users from attack.
To be eligible for the bonus, the exploit must meet the following criteria:
- It must be functional and work against Extended Stable, Stable, or Beta releases of Chrome.
- It must result in a Chrome browser sandbox escape, with a demonstration of attacker control or code execution outside of the sandbox.
- The exploit scenario must be fully remote and the exploit must be able to be used by a remote attacker.
In addition to the triple reward, Google is also offering a significant bonus for subsequent full-chain exploits submitted through the Chrome Vulnerability Reward Program (VRP). This bonus will double the regular reward.
ALSO READ:
By submitting a full chain exploit, participants could get a reward reaching as high as $180,000, potentially further augmented by other bonuses, and up to $120,000 for other exploits received throughout the rest of the six-month submission window.
“These exploits provide us valuable insight into the potential attack vectors for exploiting Chrome, and allow us to identify strategies for better hardening specific Chrome features and ideas for future broad-scale mitigation strategies,” said Amy Ressler, a Chrome Security Team Senior Technical Program Manager.
Google has been running the VRP since 2010, and has paid out over $50 million in bounties to researchers who have reported over 15,000 vulnerabilities. Last year alone, Google paid out $12 million, with a record-breaking $605,000 reward to gzobqq for a series of five security bugs part of an Android exploit chain.
The VRP is one of the ways that Google works to keep Chrome secure. By encouraging security researchers to find and report vulnerabilities, Google can make Chrome more secure for everyone.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














