Google has unveiled its best practices aimed at thwarting dangling bucket takeovers, encouraging developers to fortify their cloud environments.
The tech giant is sounding the alarm about dangling bucket attacks, a vulnerability that arises when developers remove a storage bucket while still having references to it lingering in application code, mobile apps, public documentation, or other locations.
By infosecbulletin
/ Tuesday , August 12 2025
In early August 2025, cybersecurity teams in Türkiye detected a new Java-based loader that avoided detection by all public sandboxes,...
Read More
By infosecbulletin
/ Monday , August 11 2025
ESET researchers found a zero-day vulnerability in WinRAR for Windows, tracked as CVE-2025-8088, which has been used to run malicious...
Read More
By infosecbulletin
/ Sunday , August 10 2025
A sophisticated cyber fraud has stolen over ₹5.58 crore from many bank accounts, highlighting serious concerns about digital payment security....
Read More
By infosecbulletin
/ Sunday , August 10 2025
Google confirmed that a recent data breach in one of its Salesforce CRM systems exposed information about potential Google Ads...
Read More
By infosecbulletin
/ Saturday , August 9 2025
More than 28,000 unpatched Microsoft Exchange servers are publicly accessible and vulnerable to the critical security flaw CVE-2025-53786, as reported...
Read More
By infosecbulletin
/ Saturday , August 9 2025
Google has unveiled its best practices aimed at thwarting dangling bucket takeovers, encouraging developers to fortify their cloud environments. The...
Read More
By infosecbulletin
/ Saturday , August 9 2025
Researchers revealed critical zero-day vulnerabilities that bypass Windows BitLocker encryption, enabling attackers with physical access to quickly extract data from...
Read More
By infosecbulletin
/ Friday , August 8 2025
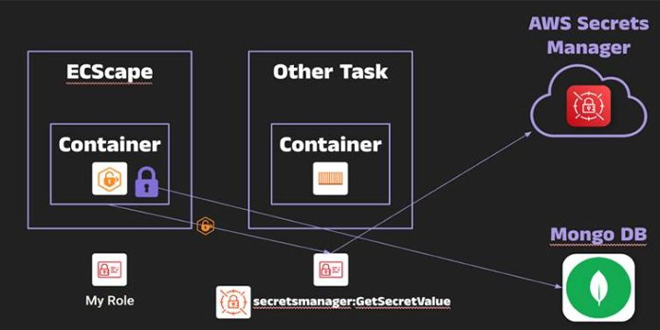
Security researchers disclosed a cirtical flaw in Amazon Elastic Container Service (ECS) that enables harmful containers to steal AWS credentials...
Read More
By infosecbulletin
/ Friday , August 8 2025
Let’s look at 7 tools for automating patch deployment. Each tool offers unique features for various environments, from small DevOps...
Read More
By infosecbulletin
/ Friday , August 8 2025
Germany's top court ruled on Thursday that police can secretly install spy software on phones and computers only for serious...
Read More
“An attacker can then simply claim the same bucket name in their own project, effectively hijacking your old address to potentially serve malware and steal data from users who unknowingly still rely on a bucket that is no longer officially in use,” the tech giant says.
Google advises a careful process for decommissioning this cloud storage and provided a four-step guide to secure unused buckets.
Google’s best practices here.
Multiple 0-days to Bypass BitLocker and Extract Data
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind