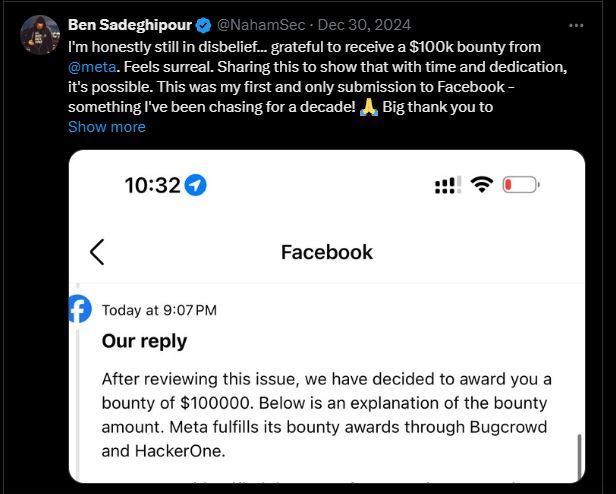
In October 2024, security researcher Ben Sadeghipour discovered a vulnerability in Facebook’s ad platform that allowed him to run commands on its internal server, giving him control over it. After Sadeghipour reported the vulnerability to Meta, Facebook’s parent company, it was fixed within an hour, and he received a $100,000 bug bounty.
Techcrunch reported “My assumption is that it’s something you may want to fix because it is directly inside of your infrastructure,” Sadeghipour wrote in the report he sent to Meta. Meta responded to his report, telling Sadeghipour to “refrain from testing any further” while they fix the vulnerability.
Sadeghipour reported that a Facebook ad server was still vulnerable to a flaw in the Chrome browser that had already been fixed. This unpatched bug allowed him to take control of the server using a headless version of Chrome to directly access Facebook’s internal systems.
Sadeghipour, who found the Facebook vulnerability working with independent researcher Alex Chapman, told TechCrunch that online advertising platforms make for juicy targets because, “there’s so much that happens in the background of making these ‘ads’ — whether they are video, text, or images.”
“But at the core of it all it’s a bunch of data being processed on the server-side and it opens up the door for a ton of vulnerabilities,” said Sadeghipour.
The researcher said he didn’t test out everything he could have done once inside the Facebook server, but “what makes this dangerous is this was probably a part of an internal infrastructure.”
“Since we have code execution, we could’ve interacted with any of the sites within that infrastructure,” said Sadeghipour. “With an [remote code execution vulnerability], you can bypass some of these limitations and also directly pull stuff from the server itself and the other machines that it has access to.”
While Meta has not provided an official comment on the incident, the substantial bounty awarded underscores the significance of Sadeghipour’s finding.
Sadeghipour mentioned that similar advertising platforms used by other companies also have vulnerabilities he has been analyzing.
This incident underscores the importance of bug bounty programs in addressing security threats. Facebook’s program, launched in 2011, has paid over $16 million, reflecting the company’s dedication to cybersecurity.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














