Researchers at cybersecurity firm SafeBreach created a new method called Pool Party. This method allows attackers to bypass EDR solutions. The researchers presented Pool Party at Black Hat Europe 2023. The experts discovered an new way to inject processes by using Windows thread pools.
Researchers found eight new process injection techniques that enable them to execute malicious code during a legitimate operation.
“The techniques were capable of working across all processes without any limitations, making them more flexible than existing process injection techniques. And, more importantly, the techniques were proven to be fully undetectable when tested against five leading EDR solutions.” reads the analysis published by the experts.
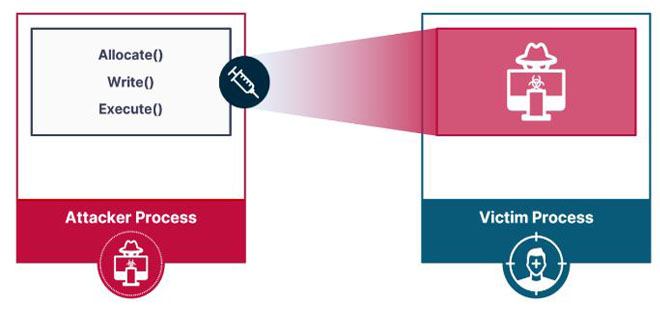
Process injection is a technique that uses three steps. First, it allocates memory in the target process. Then, it writes malicious code into the allocated memory. Finally, it executes the malicious code.
Pool Party
The researchers tested different methods and found that EDR solutions mainly detect process injection by tracking the execution method.
The experts are studying a way to make malware run by using standard computer actions. They are looking at the Windows user-mode thread pool for this possibility.
Windows processes have a default thread pool, which includes both kernel and user-mode code.
Experts believe it’s possible to exploit worker factories to achieve process injection.
A worker factory in Windows manages worker threads in the thread pool by creating or stopping them as necessary. It does not handle the scheduling or execution of work items, but makes sure there are enough worker threads available.
One of the techniques discovered by the researchers exploits the start routine of worker factories, while the other ones use the three queue types.
“Recalling the queue types, asynchronous work items are queued to the I/O completion queue. The I/O completion queue is a Windows object that serves as a queue for completed I/O operations.” continues the report. “Notifications are inserted into the queue once an I/O operation completes. The thread pool relies on the I/O completion queue to receive notifications when an asynchronous work item’s operation is completed.”
“Though modern EDRs have evolved to detect known process injection techniques, our research has proven that it is still possible to develop novel techniques that are undetectable and have the potential to make a devastating impact.” SafeBreach concludes. “Sophisticated threat actors will continue to explore new and innovative methods for process injection, and security tool vendors and practitioners must be proactive in their defense against them.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind