Mandiant has found a new vulnerability in Azure Kubernetes Services (AKS) called “WireServing.” This flaw could have let attackers increase their privileges in a compromised cluster and access sensitive credentials without authorization.
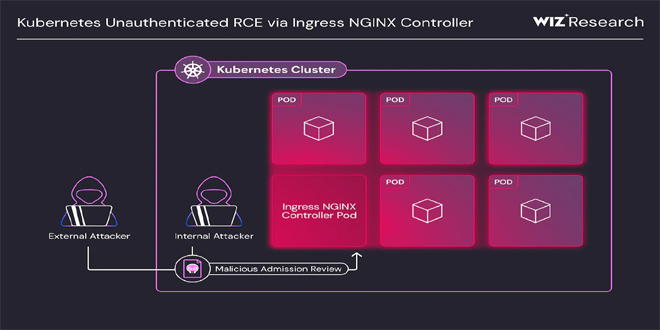
Kubernetes is a complex platform known for security challenges. A vulnerability in AKS clusters using “Azure CNI” and “Azure” for network policy allowed unauthorized access to sensitive data, including stored secrets, through a TLS bootstrap attack.
The attack didn’t need the Pod to have special permissions or host networking turned on, which makes it a big threat in environments where Pods are often deployed without strong security measures.
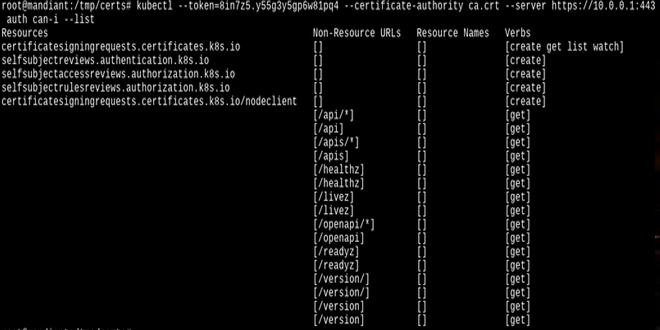
The attack targeted a vulnerability in how AKS clusters handle TLS bootstrap tokens. These tokens are important for securely connecting a node to a Kubernetes cluster. By running commands in a compromised Pod, an attacker could get the configuration files that are used to set up the cluster node. These files have the TLS bootstrap tokens and other credentials. With this information, the attacker could gain higher privileges and access sensitive data in the entire cluster.
The attack was very dangerous because it bypassed many security controls in Kubernetes environments. The attacker could access the Kubernetes API, list all nodes, and read secrets without needing root access or host networking privileges.
The attack targeted Azure WireServer, an undocumented component of Azure, and its associated HostGAPlugin. These tools, usually used for managing Azure VMs, were found to have vulnerabilities that allowed the attacker to access and decrypt sensitive configuration settings, such as TLS bootstrap tokens.
The process included asking WireServer for a decryption key, which was then used to decrypt the settings from HostGAPlugin. This uncovered the provisioning script for the Kubernetes nodes, containing the credentials for escalating privileges in the cluster.
This vulnerability has serious consequences. Attackers could get sensitive information, causing data theft, financial losses, and damage to organizations’ reputations. Exploiting this vulnerability allows attackers to do many harmful things, like accessing critical data and launching ransomware attacks.
This vulnerability shows the dangers of cloud environments with complicated setups and undocumented services which can lead to unexpected security issues. It proves that even secure environments can be vulnerable if certain services aren’t properly protected.
Microsoft acted swiftly after receiving the report from Mandiant. They released a patch to fix the issue with AKS clusters. The patch updates how TLS bootstrap tokens are handled, preventing them from being exploited. This patch restricts unauthorized access to the metadata server and blocks the exploitation of TLS bootstrap tokens.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind