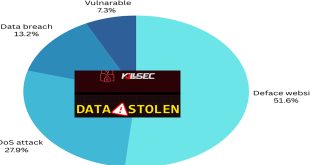
National Attack Surface (NAS) report for the first half of 2024 reveals that 56.6% of cyberattacks in Bangladesh targeted educational institutions, indicating a serious lack of maintenance and updates for school websites, making them highly vulnerable. During this period, 32.4% of attacks targeted government websites, revealing significant security flaws. The …
Read More »First Half Of 2024 Report
Prince Ransomware Hits UK and US
A new ransomware campaign is targeting individuals and organizations in the UK and US. The “Prince Ransomware” attack uses a phishing scam that pretends to be from the British postal service, Royal Mail. The Attack Methodology: Researchers at Proofpoint noticed the Prince Ransomware campaign in mid-September. The attack method is …
Read More »CISA warns active exploit of Zimbra & Ivanti endpoint manager Vulns
CISA has issued an urgent alert about critical vulnerabilities being exploited in Synacor’s Zimbra Collaboration and Ivanti’s Endpoint Manager (EPM). Organizations using these products are urged to mitigate potential risks immediately. CVE-2024-45519: Synacor Zimbra Collaboration Command Execution Vulnerability: A new vulnerability, CVE-2024-45519, has been found in the Synacor Zimbra Collaboration …
Read More »A summary of “2024 State of Cybersecurity survey” by ISACA
ISACA 2024 survey report reveals that 66% of cybersecurity professionals find their jobs more stressful now than five years ago. The annual study, sponsored by Adobe, showcases the feedback of more than 1,800 cybersecurity professionals on topics related to the cybersecurity workforce and threat landscape. According to the data, the …
Read More »
ISACA reveals
64% of Australian cybersecurity professionals feel increasing stress
A recent study by ISACA shows that almost two-thirds of cybersecurity professionals report increasing job stress. The 2024 State of Cybersecurity Survey report indicates a decline in job openings. It also reveals that 64% of cybersecurity professionals in Australia find their roles more stressful than five years ago, and 57% …
Read More »Researchers detected 31 new Malware in September
In September, cybersecurity experts discovered 31 new ransomware variants that threaten individuals and businesses. These programs encrypt valuable data, making it inaccessible, and demand high ransoms for decryption keys. This not only risks personal and sensitive information but also creates significant financial burdens for victims. Ownerd SHA-256: 519a765a3341b03a035d158605eef4620e1094f0e3d1e7be1d1ac4750f2a0552 Extensions: .ownerd …
Read More »CRI Release New Ransomware Response Guidance
New guidance on ransomware, released during this week’s International Counter Ransomware Initiative (CRI) meeting, encourages victims to report attacks to law enforcement promptly and to consult more advisors before deciding to pay a ransom. Cybersecurity experts from about 70 countries are gathering at the White House this week for the …
Read More »
ALERT
Over 700,000 Routers Vulnerable to Hack for 14 security flaws
Over 14 new security flaws have been found in DrayTek routers for homes and businesses, which could allow attackers to take control of affected devices. According to Forescout Vedere Labs,”These vulnerabilities could enable attackers to take control of a router by injecting malicious code, allowing them to persist on the …
Read More »
Patch it now!
Critical Zimbra RCE flaw exploited: Needs Immediate Patching
Hackers are exploiting a recently revealed RCE vulnerability in Zimbra email servers that can be activated by sending specially crafted emails to the SMTP server. CVE-2024-45519 is a remote code execution vulnerability in Zimbra’s postjournal service, which handles incoming emails via SMTP. Attackers can exploit this flaw by sending emails …
Read More »
CISA Warns
Network switch RCE flaw impacts critical infrastructure
CISA warns of two serious vulnerabilities in Optigo Networks ONS-S8 Aggregation Switches, which could allow authentication bypass and remote code execution in critical infrastructure. The flaws involve weak authentication, allowing users to bypass password requirements, and issues with validating user input, which could lead to remote code execution, arbitrary file …
Read More » InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind