Asus has released a crucial firmware update to address a severe vulnerability that impacts seven of its business router model. Customers are urged to promptly review their firmware status and apply the necessary updates.
The flaw CVE: 2024-3080 with a CVSS score of 9.8 is an authentication bypass vulnerability that leads unauthenticated remote attackers take control of the device. The affected routers, a series of XT8 and RT models, should now be checked for firmware updates.
By infosecbulletin
/ Wednesday , September 10 2025
Sophos fixed an authentication bypass vulnerability in its AP6 Series Wireless Access Points, preventing attackers from obtaining admin privileges. The...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Security researcher Jeremiah Fowler discovered a database containing sensitive information from gym customers and staff, including names, financial details, and...
Read More
By infosecbulletin
/ Wednesday , September 10 2025
Microsoft patched September 2025 Patch Tuesday 81 flaws, including two publicly disclosed zero-day vulnerabilities. This Patch Tuesday addresses nine critical...
Read More
By infosecbulletin
/ Tuesday , September 9 2025
Elastic reported a security incident caused by a breach at Salesloft Drift, leading to unauthorized access to an internal email...
Read More
By infosecbulletin
/ Tuesday , September 9 2025
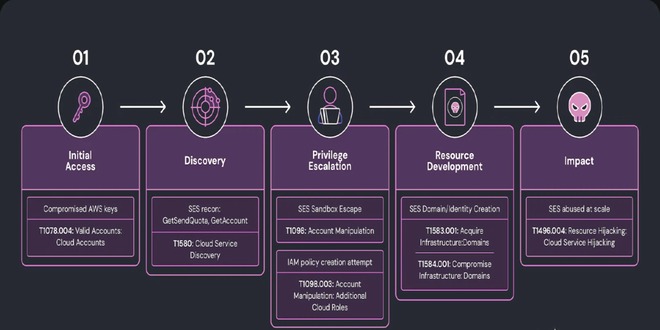
Researchers at Wiz discovered a complex phishing campaign using Amazon's Simple Email Service (SES) for large-scale attacks, showing how hacked...
Read More
By infosecbulletin
/ Monday , September 8 2025
The global ransomware landscape continues to shift in 2025, with SafePay rapidly emerging as one of the most active and...
Read More
By infosecbulletin
/ Sunday , September 7 2025
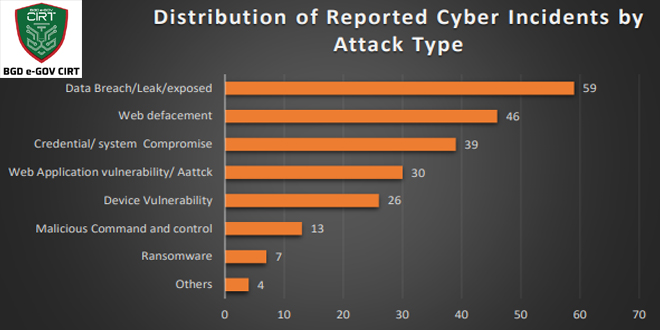
Bangladesh Cyber Threat Landscape 2024, by BGD e-GOV CIRT, reveals a sharp escalation in cyber threats across Bangladesh. The year...
Read More
By infosecbulletin
/ Sunday , September 7 2025
Investigations into the Nx "s1ngularity" NPM supply chain attack have unveiled a massive fallout, with thousands of account tokens and...
Read More
By infosecbulletin
/ Saturday , September 6 2025
ISC2 has launched a Threat Handling Foundations Certificate to assist cybersecurity experts in enhancing Digital Forensics and Incident Response (DFIR)...
Read More
By infosecbulletin
/ Thursday , September 4 2025
Jeremiah Fowler, a cybersecurity researcher, found an unprotected server revealing 378 GB of Navy Federal Credit Union files, including operational...
Read More
Asus patches seven router models:
The models affected include the following Wi-Fi 5 and Wi-Fi 6 models: XT8 (ZenWiFi AX XT8), XT8_V2 (ZenWiFi AX XT8 V2), RT-AX88U, RT-AX58U, RT-AX57, RT-AC86U, and RT-AC68U.
You can find the newest Asus firmware on their download portals. If you can’t update right away, Asus has given instructions to help protect your device. They recommend using strong passwords and disabling certain access options.
Asus has fixed another vulnerability in the update package called CVE-2024-3079. This vulnerability is a buffer overflow issue that requires admin account access to be exploited. Its severity is high, with a CVSS score of 7.2
In January, ASUS fixed a serious vulnerability (CVE-2024-3912, CVSS score: 9.8) that could allow a remote attacker to upload files and run commands on the device without authentication.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind