Google’s Threat Analysis Group (TAG) has been monitoring and disrupting Russian state-backed cyberattacks targeting Ukraine’s critical infrastructure in 2023.
Google reports that from January to March 2023, Ukraine received roughly 60% of the phishing attacks originating from Russia, making it the most prominent target.
In most cases, the campaign goals include intelligence collection, operational disruptions, and leaking sensitive data through Telegram channels dedicated to causing information damage to Ukraine.
Threat groups active in Ukraine
Google’s TAG lists three Russian and Belarusian threat actors who had notable activity in the first quarter of the year against Ukrainian targets.
The first is Sandworm, tracked by Google as “FrozenBarents,” which has focused its attacks on the energy sector across Europe since November 2022, with a highlighted case involving the Caspian Pipeline Consortium (CPC).
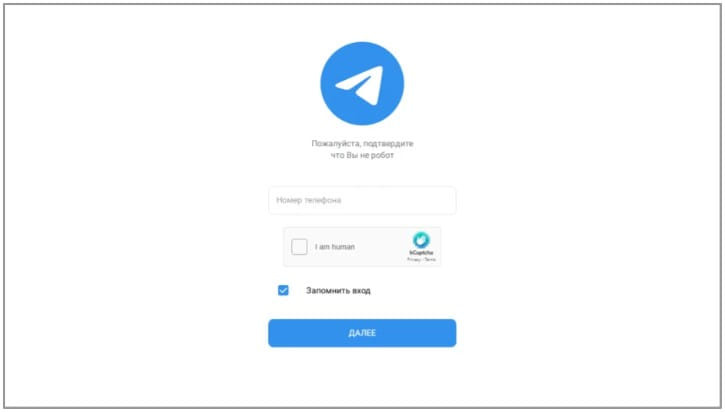
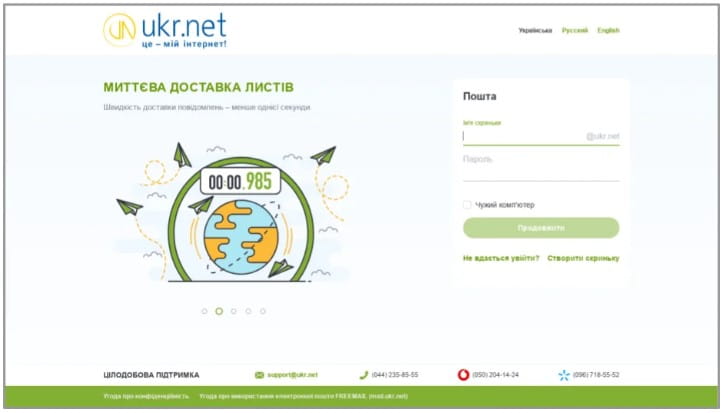
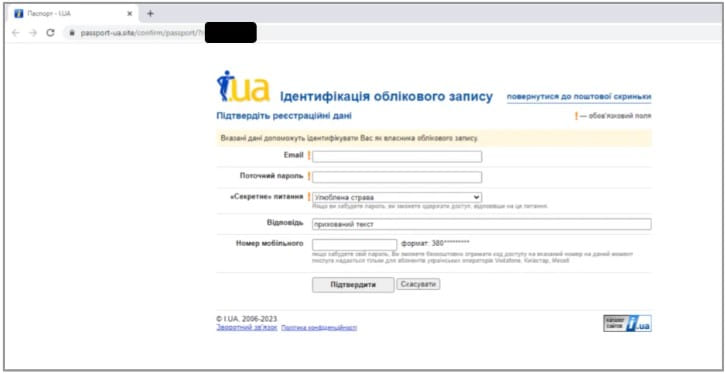
Sandworm has lately launched multiple phishing campaigns using spoofed “Ukroboronprom” websites against workers in the Ukrainian defense industry, users of the Ukr.net platform, or even Ukrainian Telegram channels.
The threat group also creates multiple online personas to disseminate false information on YouTube and Telegram, often leaking parts of the data they steal through phishing or network intrusions.
Another highly-active Russian threat actor is APT28, tracked by Google as “FrozenLake.”
Between February and March 2023, APT28 sent out multiple large waves of phishing emails targeting Ukrainians. The hackers also used reflected cross-site scripting (XSS) on Ukrainian government websites to redirect visitors to phishing pages.
This week, a joint announcement by the UK NCSC, FBI, NSA, and CISA warned that APT28 is hacking Cisco Routers to install custom malware.
The third threat actor highlighted in Google’s report is “Pushcha,” which is believed to be based in Belarus, a country that is politically aligned with the Kremlin.
Pushcha has recently launched campaigns that target Ukrainian webmail providers like “i.ua” and “meta.ua,” attempting to steal the users’ credentials by setting up phony sites.
State-funded misinformation
Google’s report also highlights cases of misinformation on its platforms, like YouTube and Blogger.
“In the first quarter of 2023, TAG observed a coordinated IO campaign from actors affiliated with the Internet Research Agency (IRA) creating content on Google products such as YouTube, including commenting and upvoting each other’s videos,” reads the Google TAG report.
The IRA (Glavset) is a Russian company linked to Wagner Group’s owner, Y. Prigozhin, engaging in online propaganda and influence operations on behalf of Russian political interests.
Google reports that it has been observing and blocking IRA-linked accounts creating content on YouTube Shorts to promote specific “news-like” narratives about the war in Ukraine to Russian domestic audiences.
All websites linked to the mentioned campaigns have been added to Google’s “Safe Browsing” blocklist, while targeted Gmail and Workspace users received alerts notifying them about malicious communications.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind