Western Digital has shut down several of its services after detecting a security breach on its network, the digital storage giant announced on Monday.
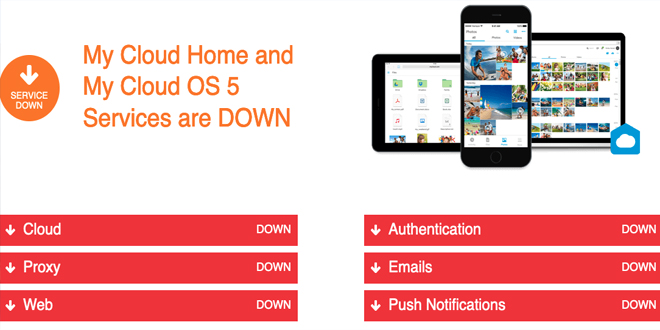
The service outage, announced on April 2, impacts cloud, proxy, web, authentication, email, and push notification services, including My Cloud, My Cloud Home (Duo), My Cloud OS5, SanDisk Ibi, and SanDisk Ixpand Wireless Charger.
By infosecbulletin
/ Wednesday , September 17 2025
Check point, a cyber security solutions provider hosts an event titled "securing the hyperconnected world in the AI era" at...
Read More
By infosecbulletin
/ Tuesday , September 16 2025
Cross-Site Scripting (XSS) is one of the oldest and most persistent vulnerabilities in modern applications. Despite being recognized for over...
Read More
By infosecbulletin
/ Monday , September 15 2025
Every day a lot of cyberattack happen around the world including ransomware, Malware attack, data breaches, website defacement and so...
Read More
By infosecbulletin
/ Monday , September 15 2025
A critical permission misconfiguration in the IBM QRadar Security Information and Event Management (SIEM) platform could allow local privileged users...
Read More
By infosecbulletin
/ Monday , September 15 2025
Australian banks are now using bots to combat scammers. These bots mimic potential victims to gather real-time information and drain...
Read More
By infosecbulletin
/ Saturday , September 13 2025
F5 plans to acquire CalypsoAI, which offers adaptive AI security solutions. CalypsoAI's technology will be added to F5's Application Delivery...
Read More
By infosecbulletin
/ Saturday , September 13 2025
The Villager framework, an AI-powered penetration testing tool, integrates Kali Linux tools with DeepSeek AI to automate cyber attack processes....
Read More
By infosecbulletin
/ Saturday , September 13 2025
Samsung released its monthly Android security updates, addressing a vulnerability exploited in zero-day attacks. CVE-2025-21043 (CVSS score: 8.8) is a...
Read More
By infosecbulletin
/ Saturday , September 13 2025
Albania has appointed the first AI-generated government minister to help eliminate corruption. Diella, the digital assistant meaning Sun, has been...
Read More
By infosecbulletin
/ Thursday , September 11 2025
On September 1, 2025, Qrator Lab identified and managed a major attack from the largest L7 DDoS botnet seen so...
Read More
In a press release issued on April 3, the company said it’s responding to an ongoing network security incident that involves an unauthorized third party gaining access to “a number” of its systems.
“Upon discovery of the incident, the Company implemented incident response efforts and initiated an investigation with the assistance of leading outside security and forensic experts. This investigation is in its early stages and Western Digital is coordinating with law enforcement authorities,” WD said.
The company is working on restoring impacted services and infrastructure. At this point in the investigation, it confirmed that the hackers did manage to gain access to certain types of data stored on its systems. The nature and scope of the compromised data is being determined.
SecurityWeek has reached out to Western Digital to find out if the attack involved ransomware and whether any customer information was compromised.
At the time of writing, WD does not appear to be mentioned on the leak site of any major ransomware group. However, even if the incident is a ransomware attack, if the intrusion is recent, the company will likely only be added to a leak website after negotiations have failed.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind