A newly found XSS vulnerability, CVE-2024-57514, in the TP-Link Archer A20 v3 Router has raised security concerns for users. CVE-2024-57514 is a flaw in firmware version 1.0.6 Build 20231011 rel.85717(5553) that lets attackers run arbitrary JavaScript code via the router’s web interface, posing a risk of exploitation.
Discovery of the Vulnerability:
The vulnerability is due to incorrect checks on the paths used for directory listings in the router’s web interface. An attacker can create a harmful URL that executes JavaScript code in the browser of anyone who visits the page. This allows harmful scripts to be injected, which can be used for phishing, session hijacking, or other attacks.
The problem is that the router doesn’t properly sanitize user input in directory listings, allowing for potential JavaScript execution. For example, a certain payload can illustrate this vulnerability:
http://192.168.0.1/<style onload=alertrvz ;>../..%2f
This URL triggers an alert box to show the vulnerability, which can be used to run more harmful scripts if desired.
Analysis and Proof of Concept (PoC):
The vulnerability permits JavaScript execution in the root directory and its sub-directories, but it does not expose cookies under the /cgi-bin/luci path because the cookie’s path attribute limits access to that directory.
Although this limitation stops direct cookie theft, attackers can still use the XSS vulnerability for other malicious activities, such as phishing or browser exploitation. Security researchers have shared a video proof-of-concept (PoC) demonstrating this vulnerability and its potential impact on unprotected users.
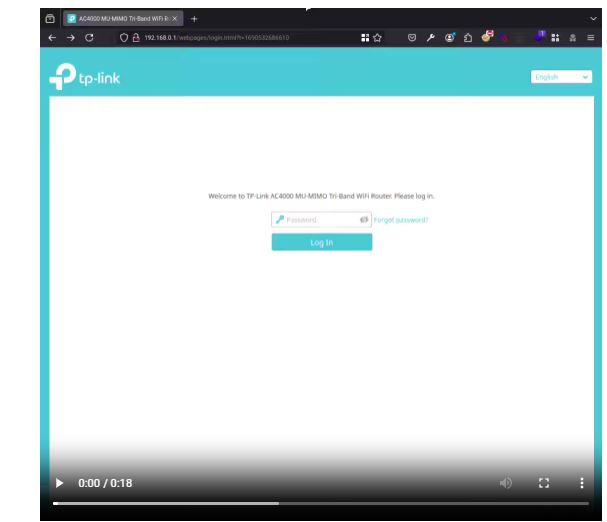
The Zyenra report states that TP-Link has confirmed a vulnerability in the Archer A20 v3 router, which has reached its End of Life (EOL) and will not receive further updates or patches.
TP-Link has chosen not to address the issue in this model due to its limited scope and severity, as assessed by their security teams. The company reassured users that they are reviewing other models for security and advised upgrading to newer, supported devices for ongoing protection.
Despite some restrictions reducing direct impact, TP-Link Archer A20 v3 router users should exercise caution.
Upgrading to a supported model is strongly recommended, as discontinued devices do not receive important security updates, making them vulnerable. Cybersecurity experts also advise against visiting untrusted links to reduce exposure to vulnerabilities.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind