MITRE Vice President Yosry Barsoum warned that U.S. government funding for the Common Vulnerabilities and Exposures (CVE) and Common Weakness Enumeration (CWE) programs ends today, potentially disrupting the global cybersecurity industry.
CVE, the more important of the two, is managed by MITRE with support from the U.S. National Cyber Security Division of the DHS. It is essential for ensuring accuracy, clarity, and common standards in discussions about security vulnerabilities.
The program is commonly used in cybersecurity tools like vulnerability management systems. It helps track new vulnerabilities using CVE Identifiers (CVE IDs) assigned by global CVE Numbering Authorities (CNAs), with MITRE serving as the CVE Editor and Primary CNA.
“On Wednesday, April 16, 2025, the current contracting pathway for MITRE to develop, operate, and modernize CVE and several other related programs, such as CWE, will expire. The government continues to make considerable efforts to continue MITRE’s role in support of the program,” Barsoum warned in a letter sent to CVE Board members.
“If a break in service were to occur, we anticipate multiple impacts to CVE, including deterioration of national vulnerability databases and advisories, tool vendors, incident response operations, and all manner of critical infrastructure.”
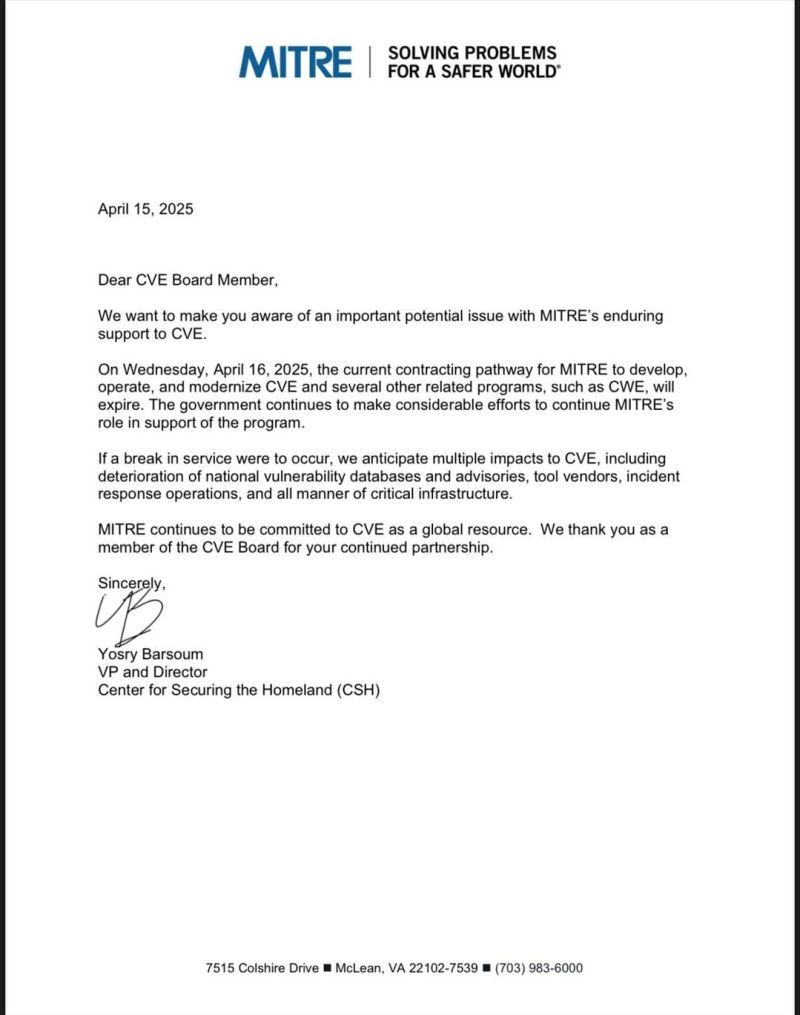
Letter to CVE Board
Letter to CVE Board (Tib3rius)
Since the letter was published online, many security experts and leaders in cybersecurity have expressed concern. They fear the program will abruptly end, leaving no standard way to track new security issues.
Former CISA head Jean Easterly warned that the immediate consequences would likely be the failure of trusted security tools and processes, leading to the collapse of global coordination efforts.
“The CVE system may not make headlines, but it is one of the most important pillars of modern cybersecurity. Losing it would be like tearing out the card catalog from every library at once—leaving defenders to sort through chaos while attackers take full advantage,” Easterly warned on LinkedIn.
“Cyber threats don’t stop at borders—and neither does defense. CVEs are the common language used worldwide to share intelligence and coordinate action. Lose that, and everyone’s flying blind.”
Casey Ellis, founder of crowdsourced security company Bugcrowd, added, “CVE underpins a huge chunk of vulnerability management, incident response, and critical infrastructure protection efforts. A sudden interruption in services has the very real potential to bubble up into a national security problem in short order.
A CISA spokesperson told BleepingComputer, “Although CISA’s contract with the MITRE Corporation will lapse after April 16th, we are urgently working to mitigate impact and to maintain CVE services on which global stakeholders rely.”
MITRE’s troubles in keeping the CVE program funded come as NIST is also scrambling to clear a large backlog of CVEs that need enrichment for its National Vulnerability Database (NVD).
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














