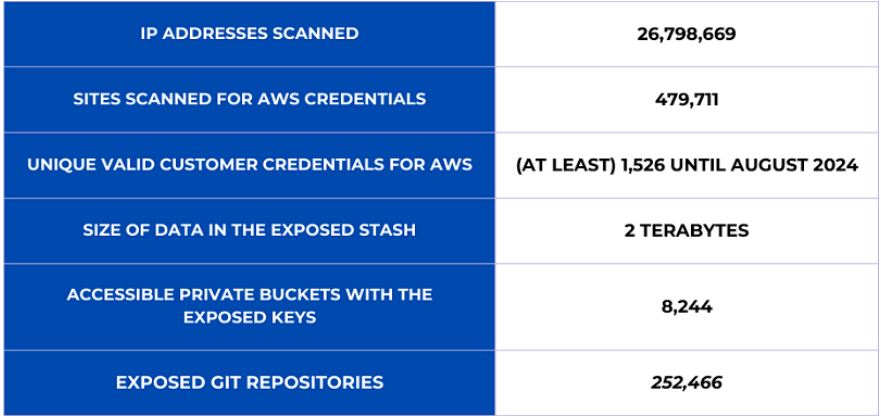
Thousands of AWS customers had terabytes of sensitive data, including personal details, AWS credentials, and proprietary code, compromised in a cyber attack linked to the ShinyHunters hacking group. They gained access to sensitive information through poorly set up systems, resulting in over 2 TB of compromised data.
Cybersecurity researchers Noam Rotem and Ran Locar discovered an operation that exploited vulnerabilities and misconfigurations on several public websites to access sensitive data illegally.
“We have identified a significant operation that scanned millions of websites, exploiting vulnerabilities in improperly configured public sites,” said researchers from vpnMentor, the cybersecurity research firm that collaborated with Rotem and Locar to publish a report on the findings. “This incident resulted in the exposure of sensitive keys and secrets, granting unauthorized access to customer data.”
The report mentioned that skilled hackers, who spoke French, used advanced tools to search the internet for security weaknesses.
“All services are operating as expected,” an AWS spokesperson said.
“AWS credentials include secrets that must be handled securely. AWS provides capabilities which remove the need to ever store these credentials in source code. For example, AWS Secrets Manager helps you manage, retrieve, and rotate database credentials, API keys, and other secrets throughout their lifecycles. Customers still sometimes inadvertently expose credentials in public code repositories. When AWS detects this exposure, we automatically apply a policy to quarantine the IAM user with the compromised credentials to drastically limit the actions available to that user, and we notify the customer. If a customer’s credentials are compromised, we recommend they revoke the credentials, check AWS CloudTrail logs for unwanted activity, and review their AWS account for any unwanted usage.”
“We found the open bucket during our own scans for misconfigured cloud environments,” Rotem said. “Our goal was to have it closed so the customer data inside would remain safe; the perpetrators from Nemesis did the same for different intentions.”
As Rotem and Locar noted in a report published Monday and shared in advance with The Register, the misconfigurations that allowed attackers to steal at least 1,526 AWS customer credentials in August alone “are on the customer side of the shared responsibility model.” Yes, they affected AWS customers. But they “could occur on any cloud service provider.”
Attackers used custom Python and PHP scripts to exploit open-source tools like Laravel to steal credentials, including Git, SMTP, and cryptocurrency keys. They stored verified credentials for later use and installed remote shells for deeper access.
AWS keys were tested for access to IAM, SES, SNS, and S3 services, allowing attackers to maintain persistence, send phishing emails, and steal sensitive data. AI service keys were excluded, probably because of outdated tools or their limited value.
Source: The register, infosecurity-magazine
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind