Vietnamese hackers are targeting businesses in Asia to get corporate credentials and financial data to sell online. Researchers at Cisco Talos found a group of hackers, known as CoralRaider, targeting India, China, South Korea, Bangladesh, Pakistan, Indonesia, and local entities with a specific type of malware.
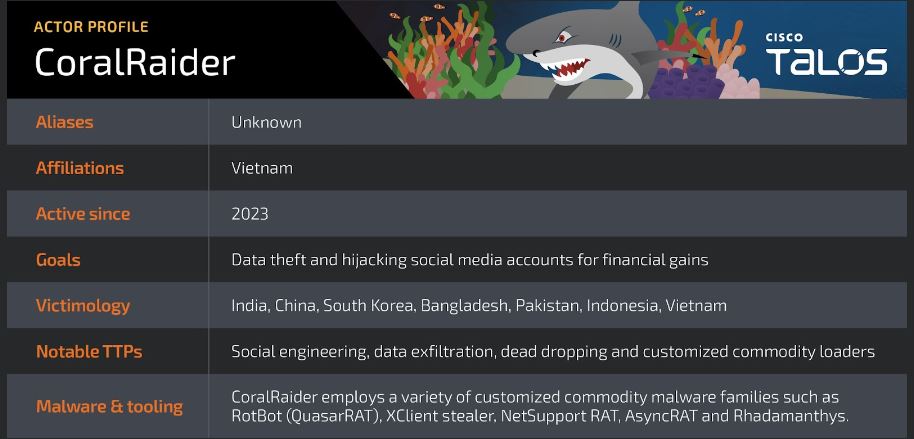
Talos believes that the group originates from Vietnam because they use Vietnamese language in their Telegram channel for controlling operations, and Vietnamese words are embedded in their code. The IP address is located in Hanoi.
Hackers use a modified remote access tool called RotBot to download an info stealer. The info stealer searches for business social media accounts with valuable data, like payment card information.

The group “focuses on stealing victims’ credentials, financial data, and social media accounts, including business and advertisement accounts,” the researchers said.
A CoralRaider attack starts when users open a harmful Windows shortcut file. This activates the infection process. Talos is uncertain about how the threat actor sends the files to victims.
The activated LNK file downloads an HTML application. This application runs a Virtual Basic script, which then runs a PowerShell script. This PowerShell script decrypts and runs three other PowerShell scripts. These scripts perform anti-VM and anti-analysis checks, bypass User Access Controls, disable Windows and application notifications, and download and execute the RotBot.
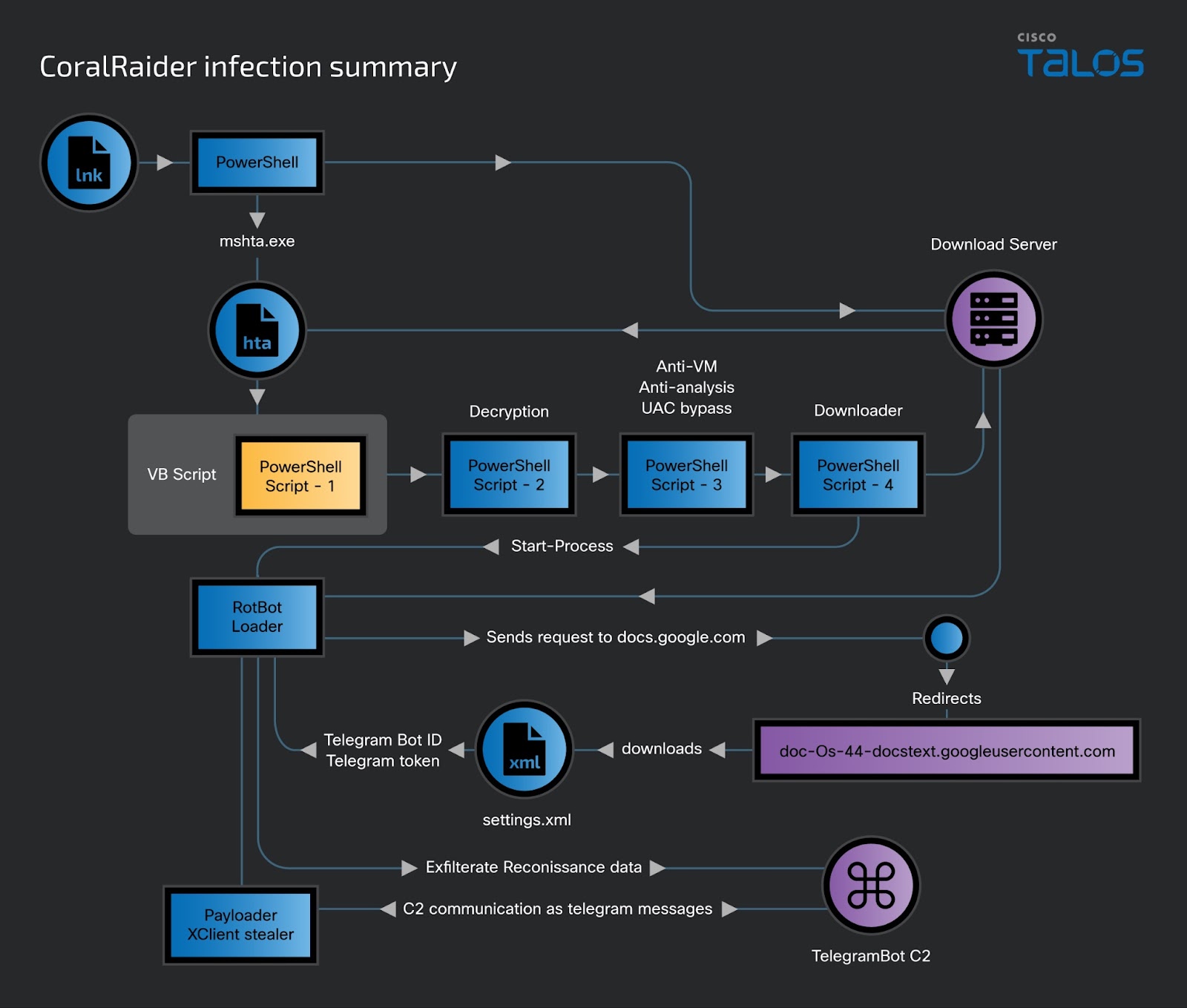
The XClient info stealer loaded by RotBot collects data including cookies, credentials and financial information from web browsers including Brave, Cốc Cốc, Google Chrome, Microsoft Edge, Mozilla Firefox and Opera, as well as Discord and Telegram.
XClient targets data from victims’ Facebook, Instagram, TikTok, and YouTube accounts. It also collects information about payment methods and permissions related to their Facebook business and advertising accounts.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














