Security researcher Matt Keeley showed that artificial intelligence can now develop working exploits for critical vulnerabilities before public proof-of-concept (PoC) exploits are released, potentially changing vulnerability research.
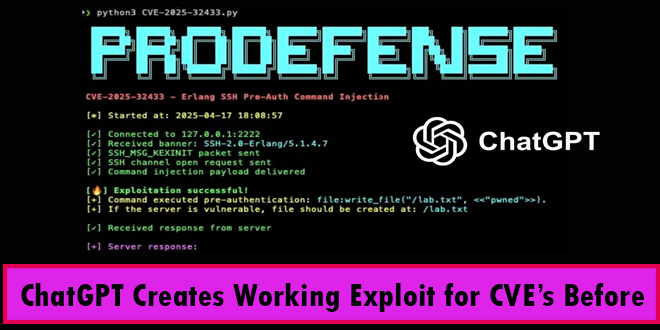
Keeley used GPT-4 to create an exploit for CVE-2025-32433, a serious Erlang/OTP SSH vulnerability rated 10.0 on the CVSS scale. This demonstrates the increasing role of AI in cybersecurity.
“GPT-4 not only understood the CVE description, but it also figured out what commit introduced the fix, compared that to the older code, found the diff, located the vuln, and even wrote a proof of concept. When didn’t it work? It debugged it and fixed it too,” Keeley explained in his detailed blog post published on April 17, 2025.
On April 16, 2025, a vulnerability was revealed in Erlang/OTP’s SSH server that allows unauthenticated remote code execution. This serious flaw occurs due to mishandling of SSH protocol messages during connection setup, permitting attackers to run arbitrary code on affected systems with elevated privileges.
Keeley started by seeing a tweet from Horizon3.ai researchers about a proof of concept (PoC) they created but hadn’t published. He then asked GPT-4 to analyze the vulnerability using this limited information. The AI systematically:
Located different versions of the code
Created a tool to diff the vulnerable and patched code
Identified the exact cause of the vulnerability
Generated exploit code
Debugged and fixed the code until it worked
“This opens up some serious questions about how quickly AI can assist in vulnerability research or even automate entire chunks of it. A few years ago, this process would have required specialized Erlang knowledge and hours of manual debugging. Today, it took an afternoon with the right prompts,” Keeley noted.
Security experts are excited yet worried about recent developments. AI makes security research more accessible, but it also allows malicious actors to create exploits more easily. Just a day after a vulnerability was announced, several researchers had already developed working exploits, with Platform Security sharing their AI-assisted proof of concept on GitHub.
Erlang/OTP versions OTP-27.3.2 and earlier, OTP-26.2.5.10 and earlier, and OTP-25.3.2.19 and earlier have vulnerabilities that have been fixed in newer releases. Organizations using Erlang/OTP SSH servers should update to OTP-27.3.3, OTP-26.2.5.11, or OTP-25.3.2.20 immediately.
This case shows how AI is changing cybersecurity. As these tools improve, the time between discovering vulnerabilities and developing exploits decreases, forcing organizations to adopt faster patching strategies
TP-Link Router Vulns Allow to Execute Malicious SQL Commands
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind