More than 84,000 Roundcube webmail installations are at risk due to CVE-2025-49113, a severe remote code execution (RCE) vulnerability that comes with an available public exploit. The flaw in Roundcube (versions 1.1.0 to 1.6.10) was discovered by Kirill Firsov and was patched on June 1, 2025.
The bug stems from unsanitized $_GET[‘_from’] input, enabling PHP object deserialization and session corruption when session keys begin with an exclamation mark.
By infosecbulletin
/ Sunday , June 29 2025
Doctors at Columbia University Fertility Center have reported what they are calling the first pregnancy using a new AI system,...
Read More
By infosecbulletin
/ Saturday , June 28 2025
Cybersecurity experts and federal authorities are warning that the Scattered Spider hackers are now targeting aviation and transportation, indicating a...
Read More
By F2
/ Saturday , June 28 2025
Since June 9, 2025, Russian users connecting to Cloudflare services have faced throttling by ISPs. As the throttling is being...
Read More
By infosecbulletin
/ Saturday , June 28 2025
A new report from SafetyDetectives reveals that hackers posted a massive 3.1GB dataset online, containing about 61 million records reportedly...
Read More
By infosecbulletin
/ Friday , June 27 2025
A 30-year-old robotics engineer from Chennai set off alarm bells in 11 states by allegedly sending hoax bomb threats. She...
Read More
By infosecbulletin
/ Friday , June 27 2025
Cisco has issued updates to fix two critical security vulnerabilities in Identity Services Engine (ISE) and ISE Passive Identity Connector...
Read More
By F2
/ Thursday , June 26 2025
CISA warns about a serious vulnerability in Fortinet FortiOS that threatens network security. CISA included CVE-2019-6693 in its Known Exploited...
Read More
By F2
/ Thursday , June 26 2025
Rapid7 has revealed serious vulnerabilities in multifunction printers (MFPs) from Brother, FUJIFILM, Ricoh, and Toshiba Tec Corporation. These findings, covering...
Read More
By infosecbulletin
/ Wednesday , June 25 2025
Citrix has issued security updates for a critical vulnerability in NetScaler ADC that has been actively exploited. The vulnerability CVE-2025-6543...
Read More
By F2
/ Wednesday , June 25 2025
SonicWall warned on Monday that unknown attackers have trojanized its SSL-VPN NetExtender application, tricking users into downloading it from fake...
Read More
Soon after the patch was out, hackers created a working exploit by reverse-engineering it and sold it on underground forums.
Though CVE-2025-49113 needs authentication to exploit, attackers assert they can acquire valid credentials using CSRF, log scraping, or brute-force methods.
Firsov shared technical details about the flaw on his blog to help defend against active exploitation attempts that are very likely to occur.
Massive exposure:
Roundcube is commonly used by web hosting providers and in sectors like government, education, and tech, with over 1,200,000 instances visible online.
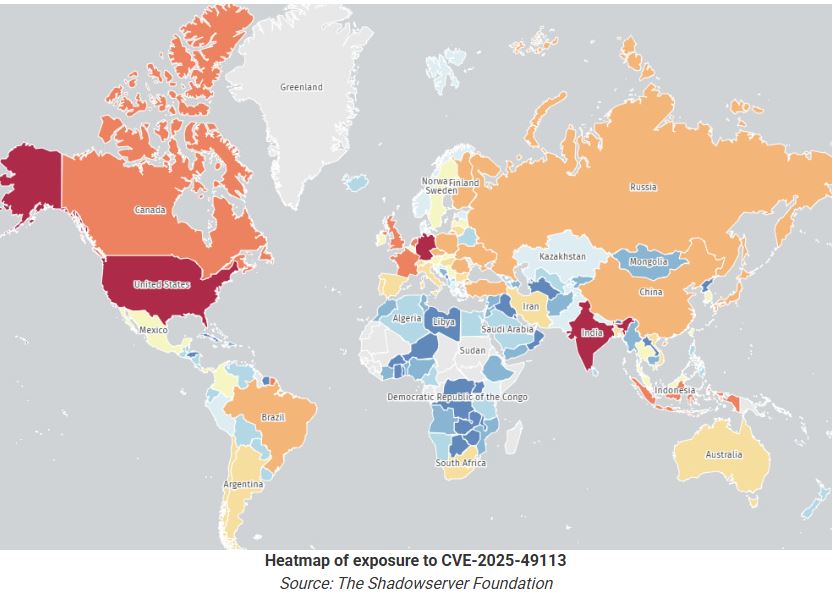
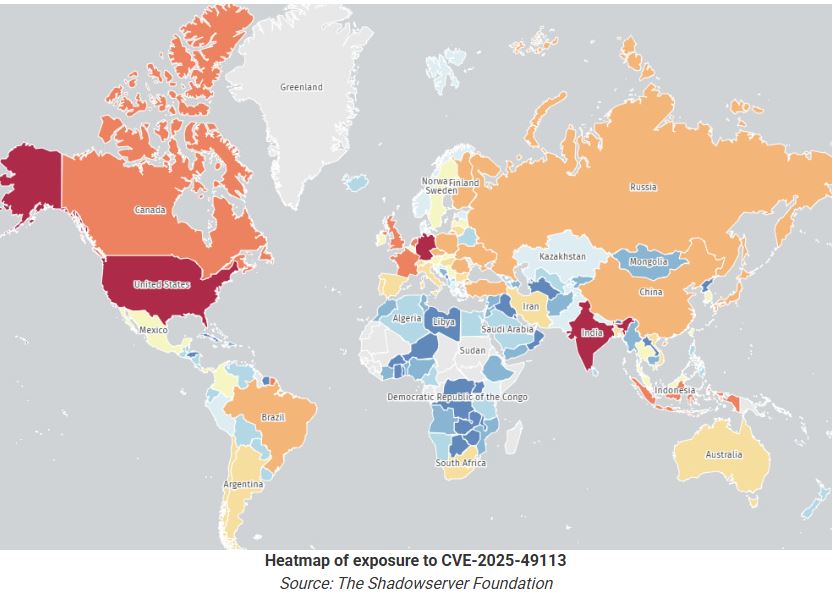
As of June 8, 2025, The Shadowserver Foundation reports 84,925 vulnerable Roundcube instances related to CVE-2025-49113.
The majority of instances are located in the United States (19,500), India (15,500), Germany (13,600), France (3,600), Canada (3,500), and the United Kingdom (2,400). The risk of exploitation and data theft makes this a serious cybersecurity issue. Admins should upgrade to versions 1.6.11 and 1.5.10 to fix CVE-2025-49113 promptly.
Bleepingcomputer reported, It is unclear if the flaw is being leveraged in actual attacks and at what scale, but immediate action is advised nonetheless.
If upgrading is impossible, it is recommended to restrict access to webmail, turn off file uploads, add CSRF protection, block risky PHP functions, and monitor for exploit indicators.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind














