In Q1 2025, VulnCheck identified evidence of 159 CVEs publicly disclosed for the first time as exploited in the wild. The disclosure of known exploited vulnerabilities was from 50 different sources.
“We continue to see vulnerabilities being exploited at a fast pace with 28.3% of vulnerabilities being exploited within 1-day of their CVE disclosure,” VulnCheck said.
In total, 45 security flaws were used in real-world attacks within a day of being disclosed. Additionally, 14 flaws were exploited within a month, and another 45 were abused within a year.
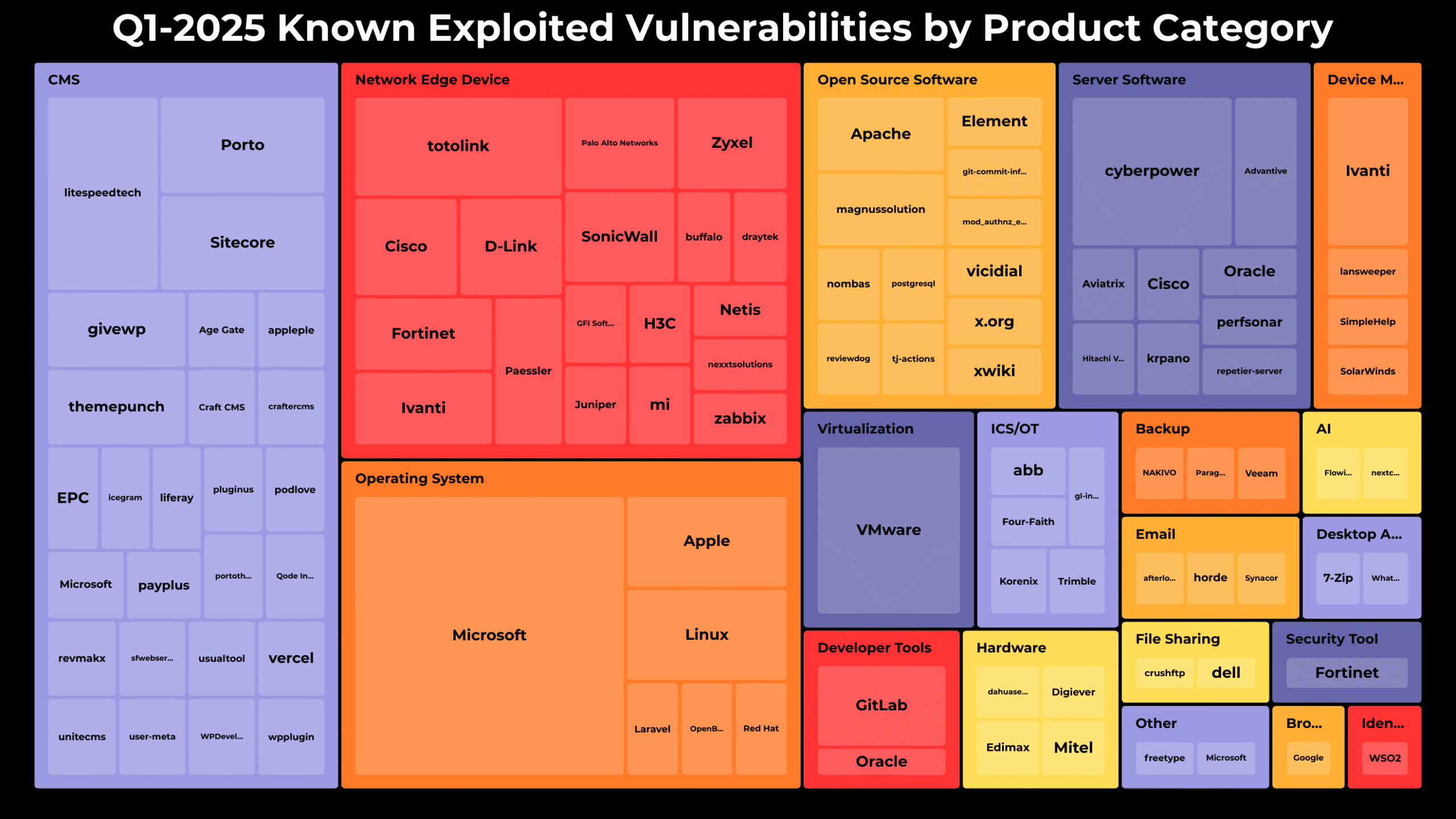
The cybersecurity company reported that most exploited vulnerabilities are found in content management systems (CMSes), followed by network edge devices, operating systems, open-source software, and server software.
The breakdown is as follows:
Content Management Systems (CMS) (35)
Network Edge Devices (29)
Operating Systems (24)
Open Source Software (14)
Server Software (14)
The main vendors and their exploited products during this period are Microsoft Windows (15), Broadcom VMware (6), Cyber PowerPanel (5), Litespeed Technologies (4), and TOTOLINK Routers (4).

“On average, 11.4 KEVs were disclosed weekly, and 53 per month,” VulnCheck said. “While CISA KEV added 80 vulnerabilities during the quarter, only 12 showed no prior public evidence of exploitation.”
Of the 159 vulnerabilities, 25.8% are being reviewed by the NIST National Vulnerability Database (NVD) and 3.1% have the new “Deferred” status.
Verizon’s 2025 Data Breach Investigations Report reveals that the use of vulnerabilities for initial access in data breaches increased by 34%, now representing 20% of all intrusions.
Data from Google-owned Mandiant shows that for the fifth year in a row, exploits were the most common initial infection method. Stolen credentials have now surpassed phishing as the second most common access method.
“For intrusions in which an initial infection vector was identified, 33% began with exploitation of a vulnerability,” Mandiant said. “This is a decline from 2023, during which exploits represented the initial intrusion vector for 38% of intrusions, but nearly identical to the share of exploits in 2022, 32%.”
That said, despite attackers’ efforts to evade detection, defenders are continuing to get better at identifying compromises.
The global median dwell time, which indicates how long an attacker remains undetected in a system, is now 11 days, up by one day from 2023.
 InfoSecBulletin Cybersecurity for mankind
InfoSecBulletin Cybersecurity for mankind